With all of the NSA, RSA and related security information privacy concerns in the news tied to if your computer systems or networks can be eves-dropped, what about your data storage?
Are you protected your data and information, along with the data storage that they reside on secure with encryption of data at rest?
If yours is like many organization to stay out of the news you might be encrypting your data protection copies for backup, business continuance (BC), disaster recovery (DR) or archive copies that go off-site on magnetic tape (or some other medium).
However what if your organization has moved beyond using tape instead leveraging hard disk drives (HDDs), nand flash solid state devices (SSD) or sending data to a cloud or managed service provider (MSP)?
For the latter, are those media/mediums also being encrypted, or has your environment fallen under the false sense of security that only magnetic tapes need to be encrypted?
I continue to find people or organizations that are under the belief that you only need to encrypt data in-flight (e.g. going to or from off-site or a cloud) or that is physically being transported somewhere else.
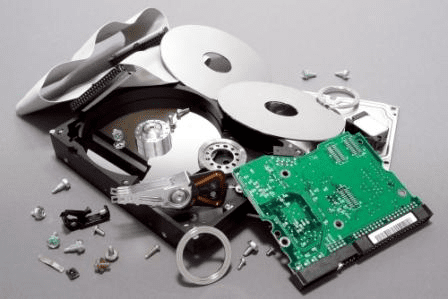
Likewise while the trend is improving, however there are still far too many laptops, tablets, workstations, PCs and other devices that do not have their HDD or SSDs encrypted, yet amazingly there are far more of these devices lost, stolen, forgotten on a daily basis vs. the headline news making occurrence of a magnetic tape being lost. The irony is that my experience has shown it is far easier to read a typical HDD or SSD than a magnetic tape, as most people do not have tape drives around.
Otoh take a PC, laptop, tablet or other device and it is relatively easy to get the drive out, access and use it.
The usual belief is that information behind firewalls and on storage attached to servers that have rights access control and identify access, all is safe; hence no need to encrypt the actual storage device.
There is a couple of other usual comments or statements that people make to me about encrypting storage devices which is that it is too difficult due to lack of good key management, and the other is that people say the encryption algorithms are no good. Both can be valid points, particular given what we are hearing with the NSA and other government activities. My usual response is a) have spare keys placed in safe trusted locations and b) do you lock the doors and windows on your home as somebody who really wants to get in probably can, hence need for multiple rings of security, however the encryption will deter the casual or more typical adversary.
Where can the storage encryption be done? Several places including via applications such as databases (Oracle, SQLserver, etc), email systems such as Exchange among others, as well as via file systems, operating systems such as Windows bit locker or third party products such TrueCrypt among many others. Most reputable backup/restore, archive and data protection or copy tools also support some form of encryption.
Encryption can also be done via appliances that sit between your server and storage systems, or storage systems, not to mention storage systems and appliances also being able to perform the encryption via software or hardware for local or even cloud access. Finally, there are self-encrypting devices (SEDs) some of which implement the OPAL standard that as their names imply, encrypt themselves with a key entrusted to a server, appliance or storage system.
For those environments that do not need encryption, there is an interesting by product of using SEDs or storage systems that have built-in encryption which is the ability to drop or destroy the keys, and depending on implementation, the drives can be instantly be effectively secure erased (to different security standard levels of course). Check with your storage system and device vendors or providers to see what they support along with the relevant standards and capabilities, as there are differences to meet various threat risks.
Walking the talk, yes, I have encryption enabled on laptops, removable and portable storage devise as well as on-site, and not to mention encrypting local backups, as well as copies sent to cloud.
There are many other server, storage I/O data protection and security topics spanning cloud, virtual and physical environments we can and will discuss in the future.
Ok, nuff said (for now).
About the author
Greg Schulz is Founder and Sr. Analyst of independent IT advisory and consultancy firm Server and StorageIO (StorageIO). He has worked in IT at an electrical utility, financial services and transportation firms in roles ranging from business applications development to systems management and architecture planning. Mr. Schulz is author of the Intel Recommended Reading List books “Cloud and Virtual Data Storage Networking” and “The Green and Virtual Data Center” via CRC Press and “Resilient Storage Networks” (Elsevier) and a four time VMware vExpert. Learn more at www.storageio.com