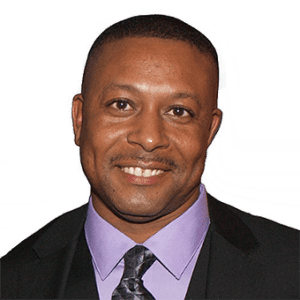
The Computer maker Acer’s U.S. webstore was breached for nearly a year, potentially exposing credit card data, names and mailing addresses of 34,500 customers. John Peterson, vice president of Enterprise Product Management at Comodo commented below.
John Peterson, vice president of Enterprise Product Management at Comodo:
 1. Practice Good Password Hygiene
1. Practice Good Password Hygiene
Create strong passwords using a hard-to-guess combination of uppercase and lowercase letters, numbers and symbols or special characters. Don’t use common names, dates, your pets’ or kids’ names, street addresses, birthday dates or other facts that attackers could easily find out about you on social media, public records or the Internet.
Also, use separate passwords for each account, and yes it’s a pain, so use a good password manager. Pay attention to reports of new breaches, and if one of the companies or sites you do business with is affected, make sure you act quickly and change your password, then be on the lookout for any signs of fraudulent activity – like odd charges, big or small, hitting your accounts, or account activity originating in other countries. Pay close attention to your email account security, since so many of your online accounts are likely to be linked to your email. Bottom line: stay aware, use strong, unique passwords and use a good password manager.
2. Educate Your Employees on Cybersecurity
Make employees aware of recent phishing scams and emails, and how those campaigns have been designed, and encourage them to create strong passwords on their accounts and periodically mandate that they change those passwords. Nobody enjoys doing this but everybody REALLY hates getting breached or divulging sensitive company or customer data. Encourage employees to report suspicious behaviors or emails. Education is critical; according to the 2015 Verizon Data Breach Investigations Report, “23% of recipients still open phishing messages, and 11% click on unknown attachments.”
3. Endpoint Security
According to Gartner Research, “44% of reference customers for EPP solutions have been successfully compromised.” The best way to prevent ‘being compromised’ is to employ a multi-layered approach to endpoint security made up of Firewall, URL filtering, Anti-Virus, File Lookup Service (FLS), Host Intrusion Protection System (HIPS), Behavior Analysis and containment with auto-sandboxing. Only with all these layers of defense in place can organizations truly be protected.







Most Commented Posts
2020 Cybersecurity Landscape: 100+ Experts’ Predictions
Cyber Security Predictions 2021: Experts’ Responses
Experts’ Responses: Cyber Security Predictions 2023
Data Privacy Protection Day (Thursday 28th) – Experts Comments
Experts Insight On US Pipeline Shut After Cyberattack
Most Active Commenters
Recent Comments
“Cybersecurity Awareness Month’s new evergreen theme "Secure Our World” is…
“Avoid storing data on personal devices: A crucial but often overlooked…
“I recommend a new nuance to passwords that isn’t often…
“In my role overseeing cloud environments and incident response, I'm…
“Cybersecurity Awareness Month serves as a reminder to confront the…