Back in March, Microsoft released data suggesting that Russian hacker groups were appearing to be preparing for a renewed wave of cyber-attacks against Ukraine, including a ransomware-style threat to organisations serving Ukraine’s supply lines.
At the time, Clint Watts, General Manager of its Digital Threat Analysis Centre said: “In 2023, Russia has stepped up its espionage attacks, targeting organisations in at least 17 European nations, mostly government agencies. Our analysis suggests that Russia will continue to conduct espionage attacks against Ukraine and Ukraine’s partners, and destructive attacks within, and potentially outside, Ukraine.”
Our own ESET Threat Report, a quarterly report that analyses the latest wave of threats impacting European infrastructure, backed up the claims. However, before we look forward, it is important to first look back.
An attack that shocked the world
In 2022, Russia’s unprovoked attack on Ukraine shocked the world, bringing devastating effects on the country and its population. Over the past year, the war has impacted everything from energy prices to sporting events.
Among the effects seen in cybersecurity, the ransomware scene experienced some significant shifts. From the beginning of the invasion, we saw a divide among ransomware operators, with some supporting and others opposing the actions of Russia. The attackers used increasingly destructive tactics, such as deploying wipers that mimic ransomware and encrypting the victim’s data with absolutely no intention of providing a decryption key.
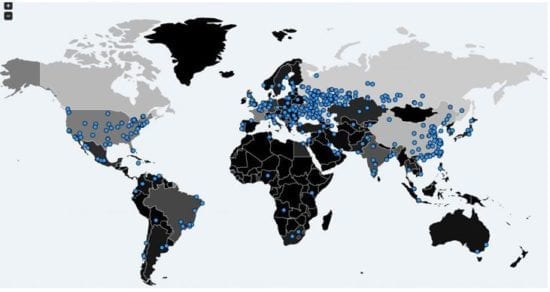
The war also affected the prevalence of brute-force attacks against exposed Remote Desktop Protocol (RDP) services, with these attacks that rose to prominence during the pandemic nose-diving in 2022. Whilst other factors might have contributed to this slump, such as the general decline in remote working, improved setup and countermeasures by company IT departments, and a new brute-force blocking feature built into Windows 11, it is telling that most of the RDP attacks detected still originated from Russian IP addresses.
The nexus for ransomware
Analysing ransomware trends more closely we can see that while detection numbers stagnated worldwide, many appeared in connection with the Russia-Ukraine war. In fact, the US Financial Crimes Enforcement Network (FinCEN) published a report a few months ago that suggested that 75% of all recorded ransomware attacks had a nexus to Russia, its proxies, or someone acting on its behalf.
At the end of last year, our researchers found a new .NET ransomware called RansomBoggs that was targeting organisations in Ukraine. It landed at the edge of the wiper category, as its early versions did have a decryption function. However, its authors added the call later, but the attribution to Sandworm – a particularly ruthless Russia-aligned APT group – suggests its victims are alas unlikely to be helped by the malware’s operators. We base this attribution on an almost identical POWERGAP PowerShell script used to distribute RansomBoggs and earlier Sandworm malware CaddyWiper, both deployed via Active Directory Group Policy. Prestige ransomware, another malware from this category, was also detected targeting logistics companies in both Ukraine and Poland.
Over-writers and wipers
Ransomware-mimicking wipers proved especially popular in connection with the Russia-Ukraine war. There is no doubt that the conflict has highlighted its destructive potential, as threat actors on both sides of the conflict have used ransomware variants to attack their adversaries’ organisations and effectively wipe their data by encrypting it with no intention of providing the decryption key.
In the last few months of 2022, several new strains were launched that fit into this “wiper mimicking ransomware” category or were at least at its edge. In October, a wiper called Azov Ransomware started spreading. It overwrote 666-byte chunks of data at a time, with no chance of recovery. Azov also backdoored most of the 64-bit executables it could find, increasing the risk of it being spread further. In the ransom note, its creators criticised the lack of Western help for Ukraine and sent political messages to the western public asking them to start protests. However, as the malware did not target any Russian organisations, it is likely a false flag operation.
In November, several organisations in Ukraine were then hit with the Somnia wiper. CERT-UA attributed the malware to a group known as From Russia with Love. Supporting this view is an image dropped by Somnia’s first-stage executable, displaying the name of the group and the letter Z – famously used as a symbol of Russian aggression against its neighbour.
In December – probably in retaliation for the Somnia attacks – CryWiper was launched at Russian governmental agencies and courts, destroying their data and systems. It is worth noting that CryWiper is only the second known destructive malware targeting Russia since the war broke out, with RURansom in March 2022 being its sole predecessor.
Driving a wedge
The Russian invasion of Ukraine has driven a wedge between actors in the ransomware scene, dividing them into supporters and opponents of the aggression. While the rift has led to catastrophic leaks, in some cases including source code and private conversations of the gang members, it has also motivated attackers to deploy increasingly aggressive methods, to insult their victims, and sometimes even to destroy their data. This will only increase this year.
These ideological fights have not influenced ransomware developments as much as you might think, though. Most threat actors have continued with the double-extortion scheme and compromised organisation they felt could afford to pay a ransom. Consumers remained mostly uninteresting for the ransomware scene, with the only exception being the owners of NAS devices. As for amateurish ransomware attempts, 2022 was rife with these, with a large chunk of them being written in Python.
In the coming months, we expect the saturated ransomware scene to become even more feisty and competitive, with tensions building between individual ransomware gangs – part of it due to ideological differences and disagreements linked to the war. As defenders, we hope those clashes will lead to threat actors losing their focus and making mistakes that can be leveraged to create decryptors, or in the best-case scenario, lead to their arrest and prosecution.
Dilki Rathnayake is a cybersecurity content writer and the Managing Editor at Information Security Buzz, with a BSc in Cybersecurity and Digital Forensics. She is skilled in computer network security and Linux system administration. Dilki has also led awareness programs and volunteered for communities promoting best practices for online safety.
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.