Trustwave has discovered the popular Extendoffice.com Microsoft product site has begun redirecting people to the Angler Exploit Kit again, leaving many users still exposed to the TeslaCrypt ransomware.
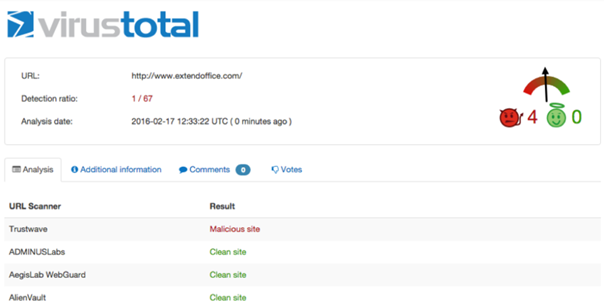
The exploit was initially closed last week after Trustwave discovered it, but has reappeared. According to the Google analytics tool VirusTotal, only one URL scanning engine (Trustwave SWG) is flagging the URL as malicious at the moment.
[su_note note_color=”#ffffcc” text_color=”#00000″]Trustwave:
They say that with great power comes great responsibility. In the world of websites the more popular your website is the greater your responsibility, and being responsible means, amongst other things, keeping your systems up-to-date.
We’ve recently come across an unfortunate case where a fairly popular website was redirecting its visitors to the Angler Exploit Kit which, upon successful exploitation, dropped the TeslaCrypt ransomware on the victim machine.
This blog post should serve as a reminder for all of the web admins to keep their web applications up-to-date, as well as a cautionary tale of what might otherwise happen, told through the story of www.extendoffice[.]com.
“extendoffice” sells add-ins to Microsoft office and it also provides “Tips and Tricks” for Microsoft Office users. It is ranked in Alexa’s top 10,000 globally, and approximately rank 5,500 in the US. These numbers may not sound impressive, but considering the millions of websites out there in the world, any site with those kind of rankings is likely getting over a million visitors per month; in the world of exploit kits that is a lot of traffic.
Our tale begins a few days ago, as we were going about our daily work looking into telemetry data from our products. We noticed the redirection of visitors from the “extendoffice” site to the Angler Exploit Kit. With Malicious advertising being popular as it is in the world of exploit kits, such a sight isn’t entirely unheard of, but upon further investigation we saw that this behavior goes back as far as February 6th and decided to investigate further.
Browsing to the homepage of “extendoffice” shows an error message at the top of the page, which always raises suspicion to a security researcher:
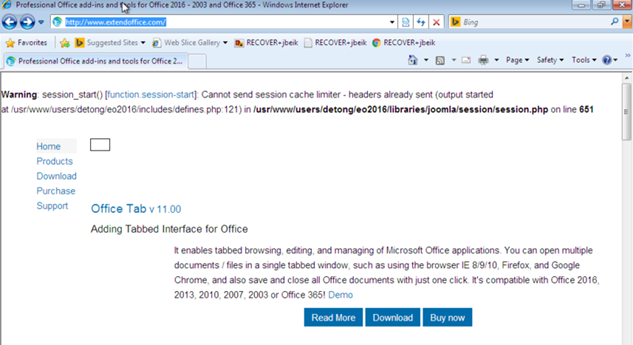
According to the error message it’s easy to see that it is a Joomla-based site, further checking reveals that it is using Joomla version:
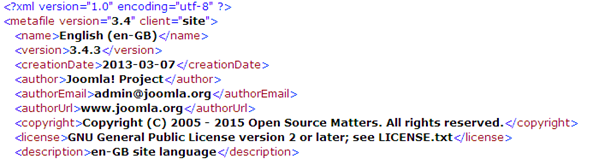
Unfortunately, this version is vulnerable to CVE-2015-8562 “Object Injection Remote Command Execution” – a vulnerability that was exploited in the wild as a 0day before it was patched on Dec 2015 with the release of version 3.4.6 of Joomla. We believe that the cyber criminals behind the attack used this vulnerability to upload a malicious script to extendoffice’s web server, which then injected obfuscated JavaScript code to every web page displayed to visitors:

De-obfuscating the script reveals another layer of obfuscated JavaScript code with two interesting parts:
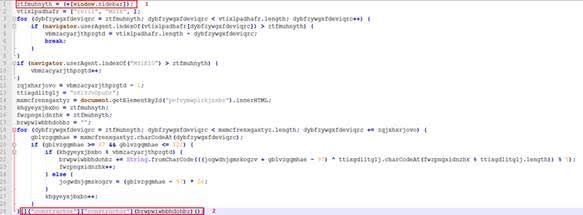
It’s no secret that cyber criminals and the security community are playing an endless game of cat and mouse, this time we found some interesting tricks in the deobfuscated code which were likely used in order to deceive and bypass security scanning engines:
- stkvphvshha = (+[window.sidebar]);
Running this line of code on IE returns the number 0 (zero) which is later used as a counter in a deobfuscation loop. Running the same line of code on Firerfox, however, returns NaN (Not a Number)- which basically breaks the flow of the code. We believe that by choosing this “sophisticated” method to assign the number 0 to a variable, the authors of this code aimed to bypass security scanners which use Firefox’s JavaScript engine SpiderMonkey (open source) to scan web pages. Because Angler targets mainly Internet Explorer users, they wouldn’t be losing any “valuable” traffic with this technique.
- Obfuscated JavaScript code is usually designed such that during runtime an obfuscated string is de-obfuscated into a string that represents JavaScript code. This code is then executed using the “eval” method. The use of “eval” often raises flags for security scanners and so cyber crooks are constantly trying to come up with new ways to avoid explicit usage of this method by searching for creative replacements. In this instance they use a very interesting technique to execute a string avoiding eval:
[][“constructor”][“constructor”](<string representing JavaScript code>)()
In JavaScript the “constructor” property returns the prototype of an object. In this case the prototype of [] is the Array class. Accessing the “constructor” property of the Array class returns the Function object. The constructor of Function object then returns a function and the body of that function is the last parameter, which is passed to the constructor. This results in the creation of a function that uses the provided string as the function’s body (i.e. code), which is then instantly executed. Using this creative way they’ve managed to execute a string without using eval.
For more information visit HERE.
De-obfuscating the second layer of JavaScript code finally reveals the injected iframe that leads to Angler EK landing page:

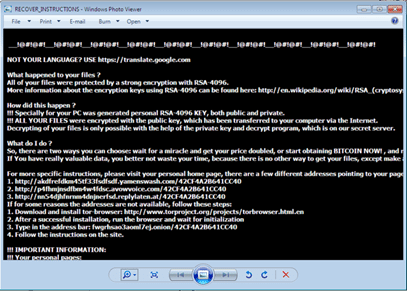
Down the road of a “successful” exploitation scenario lurks the notorious TeslaCrypt ransomware, demanding that a ransom be paid in order to decrypt the now-encrypted files on the victim machine:
The scariest thing about this incident is that a quick URL scan on VirusTotal shows that this incident has gone largely unnoticed:
Unfortunately, as end users we have no control over the safety measures taken by websites to secure our visit to them, but by keeping our software up-to-date we can make sure that our attack surface remains minimal.
For enterprises, it is important to have security products in place that are able to deal with these threats and protect corporate users.
We have been actively working to protect users against this attack; we’ve notified “extendoffice” as well as their hosting company regarding this incident. At the time of publishing of this blog post we have received no response from either one. However, as of a few hours ago, it appears that the website has been cleaned and is no longer redirecting users to the Angler exploit kit. We will continue to monitor the situation, as we have no official confirmation regarding who or what resolved it.
Trustwave Secure Web Gateway protects its customers against this attack and the Angler Exploit Kit in general.[/su_note]
[su_box title=”About Trustwave” style=”noise” box_color=”#336588″] Trustwave helps businesses fight cybercrime, protect data and reduce security risk. With cloud and managed security services, integrated technologies and a team of security experts, ethical hackers and researchers, Trustwave enables businesses to transform the way they manage their information security and compliance programs. More than three million businesses are enrolled in the Trustwave TrustKeeper® cloud platform, through which Trustwave delivers automated, efficient and cost-effective threat, vulnerability and compliance management. Trustwave is headquartered in Chicago, with customers in 96 countries.[/su_box]
Trustwave helps businesses fight cybercrime, protect data and reduce security risk. With cloud and managed security services, integrated technologies and a team of security experts, ethical hackers and researchers, Trustwave enables businesses to transform the way they manage their information security and compliance programs. More than three million businesses are enrolled in the Trustwave TrustKeeper® cloud platform, through which Trustwave delivers automated, efficient and cost-effective threat, vulnerability and compliance management. Trustwave is headquartered in Chicago, with customers in 96 countries.[/su_box]
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.