It was in 1989 when Clifford Stoll first published The Cuckoos Egg, and in my opinion this is not only the best ever book written on the subject of Cyber (then IT) crime, but is also a must read for any person who aspires to join the world of Cyber Security. The book was also possibly the first ever serious factual account of cyber crimes, electronic incursion and state sponsored hacking. What is an amazing fact however is, the presented events in this fine read were detected from, what amounted to a tiny accounting deficiency of just 75-cents of unaccounted Unix computer time. Clearly, now hence 31 years ago since the publication of this amazing piece of computer-crime history, we may compare its observed discoveries to events derived from today’s landscape of complex computerisation and the associated levels of crime, and one observation is for certain – the discoveries of the Cuckoos Egg from all those years ago, when compared to today’s landscape of insecurities and successful hacks, as serious as they were in the day, are a but a drop in the electronic ocean of cyber adversity in the year 2020 when we see everything from the Government to Banks being successfully hacked on a very regular basis!
In my humble opinion, what has driven today’s electronic insecurity of our wired planet even closer to the edge of a lights-out condition is the embracement of low cost technology, which at the outset represented the quantum shift towards the awaiting hands of criminality, and state sponsored actors. It was the move away from centralised trusted management and compartmentation of mainframe systems, morphing over to jump into an untidy bed with COTS (Commercial Off The Self) applications and systems that accompanied the levels of future exposures. This along with the growth of interconnectivity between systems was not always found to be comparable to the previous models of the secure state of the historical computer platforms architecture. One example of such robust security was the limitations imposed by LU62, with its obscure RFC-1918 type non-routable protocols – and not forgetting Windows NT with its assured level of security (so long as it was not networked!). However, we were by natural technological evolution in pursuit of interconnectivity, collaboration and flexibility tripping toward a much enhanced favourable position for feeding the world of the hacking communities with a very tasty set of new possibilities upon which they could practice their dark arts – a shift toward Cyber Insecurity making its first appearance in real time. Add to this the increased usage of the aforementioned COTS (Commercial Off the Shelf) applications and systems, and possibly now with hindsight we can see the maiden voyage on cyber-instability setting sail for new insecure horizons to come!
In those early dangerous days, my own operational environments were within the confines of a US driven SCIF (Sensitive Compartmented Information Facility) born out of departments of the Director of Central Intelligence Office and the published Directive 6/3 relating to protecting sensitive information assets – in these environments we were not only working to the ORANGE Book, and every other publication of the Rainbow document set, but here, there was another step toward total security lock-down which denied any external wired interface enjoying egress from the SCIF environment. And with every single person also being subjected to High Level Security Clearance, with the additional requirement to be read into every compartment where access would be granted, on the human side of Personal Security we were well covered. However, by comparison to the Commercial World where there were brave advancements toward deploying globalised an on-mass state of interconnectivity, we were an isolated example of a robust security posture!
Going back to the book itself, the lines below written so long ago would seem to resonate and translate into the present 2020 surface of cyber exposures, and also bring to mind possibly just how far the modern day of cyber-security (insecurity) has fallen onto a known-known historic digital sword:
“The cuckoo lays her eggs in other birds’ nests. She is a nesting parasite: some other birds will raise her young cuckoos. The survival of the cuckoo chicks depends on the ignorance of other species.”
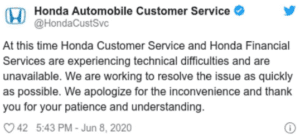
So, now apply the above statement extracted from the book to the cyber situation we meet on a very regular basis in our modern times, with such predominant frequencies of attacks occurring. In fact, it makes more sense to ask who has not been hacked, rather than who has – and even as I sit and write this small brain-dump this week I read that Honda has suffered a global cyber event implicating multiple systems across their business areas – See Fig 1 below.
Fig 1 – Honda Tweet
The depth and breadth of the Cuckoos Egg is based on how Serious and Organised Criminals and Government Intelligence Agencies were able to leverage the, then new era of interconnected systems, such as, for example US government to academic interfaced networks to worm through the interconnected electronic opportunities to locate the point of computerised interest to compromise or manipulate. But the real point of the focus of Stoll’s book for myself is the lack of defensive vision – something which is suffered by many companies today. In this scenario, given there was an awareness that the Shadow Password File had been acquired from a Unix system, it was not considered to be a threat to the security posture as it was encrypted. Just to expand on this, on Unix/Linux operating systems, the shadow password file is a system file in which the user passwords are stored in a secure format so that they are not available or exposed to unauthorised access. Thus, ordinarily, user information, including passwords, are/were kept in a system file at location ‘/etc/passwd’. The password for each user is stored in an encrypted form, which some would consider to be only in an encoded form since it was not really encrypted by a robust algorithm.
However, much akin to the threats posed by the known-known dangers of OSINT (Open Source Intelligence) in 2020, the system owners at the time did not consider the real potential opportunity for insecurity to manifest, and did not take into account that once a potential adversary has gained access to the nest in which sensitive egg’s reside, such a valuable file containing all the passwords was in an encoded form should raise an obvious red-flag to take some proactive defensive steps to, at the very least change passwords which grant access to high-value sensitive systems. The point that was missed way back then was, once a sensitive file has been acquired and is in the off-line hands of a potential attacker, they are then by inference granted all the time they need to work the objects protected content into an insecure form for onward exploitation – or, in OSINT terms exploit its valuable sources of intelligence to whatever end the attackers intention is!
The concluding rhetorical question I have about Mr Stolls Cuckoos Egg is, what did it teach us over the past 30+ years – and sadly I have to answer ‘it would seem very little!’ Not only do we seem to have stumbled along a path littered with the pre-warned egg-holes, have wandered into a world of IoT (Internet of Things), or on occasions more a case of IoUT (Internet of Useless Things) – and all this associated with a dire record of insecurity, ranging from regular banking outages, on-mass loss and compromise of subject data records on an almost daily basis, not to mention a cyber-crime bill approaching, if not exceeding a global representational value of trillions of dollars, the CV so far is not looking good for the future of what we now term Cyber Security. Now add to this, post Cuckoos Egg era, the lack of qualified, skilled and aware back-to-basics professionals who understand the nuts-and-bolts part of the cyber-security equation, along with the march of boot-camp driven fledgling professionals equipped with their pan and pad to commence their tick-box exercise, I can only despair for where the world of Cyber Security is really going.
Looking over my multiple years within both Military and Commercial worlds of operations, I have noted the move toward the over reliance on Compliance and Governance led operations, at the expense of what would seem to be the dying days of back-to-basics. Whilst I do of course understand and accept the necessity to enable both compliance and governance within the operational environment, I am hopeful that the dire state cyber security in our current times does send a red-flag message up to the higher level of the business to remind them that something may be missing in their security plan – maybe its time to go out and purchase a copy of the Cuckoos Egg to to reflect and compare its aged content to the year of 2020 and beyond, and learn from the past before it is too late!
Just in case you are inspired to read the book it is at the following ISBN reference points:
ISBN-13: 978-1-4165-0778-9
ISBN-10: 1-4165-0778-7
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


