As enterprises acquire more and more IT systems, many of which are no longer hosted internally, users are having to deal with additional authentication requirements and multiple complex passwords.
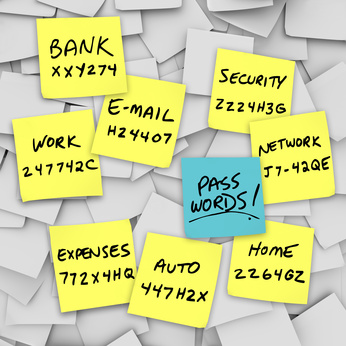
Every company has individuals who put their passwords on Post-Its stuck to their monitors, who try to reuse the same few passwords for everything, and who do not log out to avoid having to re-enter data the next day. Most of us have implemented policies to try and eliminate this type of behaviour, but it stills persists, leading to increased security and compliance risks.
However, users who endeavour to follow security policy but frequently forget their passwords create a different problem. In organisations Fordway has surveyed, these types of users can lead to more than 25% of all Service Desk calls logged. Finding a way to reduce this would increase productivity and reduce costs.
Featured Download: Social media access at work. Do your employees know the rules?
The ultimate solution would be single sign-on. In the past, these solutions have been highly complex and required significant investment. However, the cloud now offers an opportunity to provide a solution that can be used to authenticate against almost all IT services available today, from ERP and CRM systems to the public cloud.
The solution works by providing a central account or identity and provisioning this into target systems, e.g. Active Directory, SAP, etc. This manages user authentication and entitlement (depending on their role) as well as compliance, and it provides user self-service. Adding the cloud enables single sign-on to web service issues and access to on-premise applications from any location. It also configures the system to act as an IDP for cloud/extranet services and SAML.
Secure single sign-in to all key corporate systems from any location using a cloud-based solution offers three key benefits.
First, it enhances application security by externalising authentication and authorisation to applications, web resources, web services and data. This protects systems from direct exposure. Multifactor authentication could then be added as an additional level of security.
Second, it improves compliance. Having a single secure login standard and basing access to all systems on established policies and audited practices eliminates non-secure user practices and ensures all systems have compliant authentication levels. By providing complete visibility into identity and access management and providing a formal audit trail, it can help organisations achieve and maintain compliance.
Thirdly, by providing user self-service for routine issues it can increase productivity and reduce costs, freeing up Service Desk staff to work on other issues.
Clearly, any cloud-based access solution is only as good as the hosting company’s own cloud security. However, most cloud service providers implement and manage considerably better IT security controls than internal IT departments. Their businesses depend on it, they may have pan-government security accreditations that require them to be regularly tested, and they can afford the best security technologies and staff to maintain and update them. For medium-sized companies, cloud-based authentication could be a significant aid to productivity and security, as well as help free up budget space for other uses.
For more information visit .
By Richard Blanford, Managing Director, Fordway
 Bio: Richard founded Fordway in 1991 and has built it into one of the UK’s most respected IT infrastructure change providers. An ex-technician, his 20+ years’ experience enable him to prioritise business-critical problems and offer constructive, vendor independent advice.
Bio: Richard founded Fordway in 1991 and has built it into one of the UK’s most respected IT infrastructure change providers. An ex-technician, his 20+ years’ experience enable him to prioritise business-critical problems and offer constructive, vendor independent advice.
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.