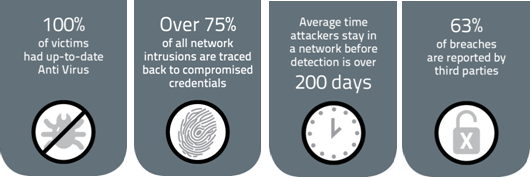
The evidence from 2015 is clear: traditional signature-based end-point protection is ineffective against the modern attack, which is persistent and targets zero-day vulnerabilities. Here are some factoids for consideration:
Today organizations are facing threats that are more complicated and move too quickly for traditional information security tools to address. Attackers that seek only to disrupt business have targeted organizations with multi-layered attacks, which have come to be known as advanced persistent threats (APTs). The  common thread that exists in these types of campaigns is the use of customized malicious code to gather and facilitate the exfiltration of your data to the attackers. It has become quite easy (and de rigueur) for attackers to modify generic malware such that its MD5 or SHA checksum differs and thus defeat many traditional signature-based defenses. It is quite common for the malware to establish persistence by spreading laterally and/or copying itself to multiple locations on the infected system.
common thread that exists in these types of campaigns is the use of customized malicious code to gather and facilitate the exfiltration of your data to the attackers. It has become quite easy (and de rigueur) for attackers to modify generic malware such that its MD5 or SHA checksum differs and thus defeat many traditional signature-based defenses. It is quite common for the malware to establish persistence by spreading laterally and/or copying itself to multiple locations on the infected system.
Once the malware infection is established, the normal pattern is to spread  laterally from less to more valuable systems. This can be observed as spreading through file shares that may be in use across departments, or by the unexpected use of remote access (for example RDP in Windows or ssh in Linux environments). In many cases, the spread is also as an e-mail; the malware determines a list of correspondents and mails a copy of itself apparently from the infected user. This has the benefit of being from an apparently trusted sender. The rise of Windows 7/8/10 in the network has also encouraged attackers to use WMI, a very powerful and now native mechanism used for Windows Update. It is quite common that even up to date signature based anti-virus solutions do not detect these infections. This is also a pattern to establish persistence. If found on one system or location, there are other copies and full eradication becomes harder.
laterally from less to more valuable systems. This can be observed as spreading through file shares that may be in use across departments, or by the unexpected use of remote access (for example RDP in Windows or ssh in Linux environments). In many cases, the spread is also as an e-mail; the malware determines a list of correspondents and mails a copy of itself apparently from the infected user. This has the benefit of being from an apparently trusted sender. The rise of Windows 7/8/10 in the network has also encouraged attackers to use WMI, a very powerful and now native mechanism used for Windows Update. It is quite common that even up to date signature based anti-virus solutions do not detect these infections. This is also a pattern to establish persistence. If found on one system or location, there are other copies and full eradication becomes harder.
 Eventually, malware will ex-filtrate the sensitive data to the attacker outside the network. This can be observed by careful examination of network traffic going from known systems inside the network to unknown endpoints outside the network. Sometimes, the outside endpoints are of poor reputation (i.e., have been observed to be involved in malicious activities) but more often are unknown to typical threat intelligence feeds. It is a relatively simple matter for attackers to obtain public IP addresses and avoid association with known bad domains. Therefore, malware often sends its data to bare IP addresses. This has the added benefit of avoiding any proxy rules that may be configured.
Eventually, malware will ex-filtrate the sensitive data to the attacker outside the network. This can be observed by careful examination of network traffic going from known systems inside the network to unknown endpoints outside the network. Sometimes, the outside endpoints are of poor reputation (i.e., have been observed to be involved in malicious activities) but more often are unknown to typical threat intelligence feeds. It is a relatively simple matter for attackers to obtain public IP addresses and avoid association with known bad domains. Therefore, malware often sends its data to bare IP addresses. This has the added benefit of avoiding any proxy rules that may be configured.
So how does the modern IT manager defend effectively (and efficiently – since cost is always a concern) against this threat landscape?
The answer is in a suite of technologies now called endpoint threat detection and response (ETDR or EDR). These are IT analytics solutions which provide visibility and insight into abnormal behavior that could represent potential threats and risks and enable enterprises to improve their security posture. A sensor at the endpoint is used to detect the launch of new processes and compares the MD5 (or SHA) hash of this process to determine if it has been seen before/trusted. This trust list can be quickly established from a baseline which includes the vast repository called the National Software Reference Library (www.nsrl.nist.gov)maintained by the US Government (www.nist.gov) and supplemented by locally known trusted applications.
Detecting ex-filtration is also best done from the endpoint because the sensor can pinpoint the specific application. Typical techniques are to have non-browser applications use standard outbound ports or standard browser applications communicate on non-standard ports. The communication is done sporadically and in small volume to avoid spikes which are observed by network analyzers.
The fact is that traditional defenses are well known to attackers and new malware strains are impervious to them. This includes signature based anti-virus, traditional signature based Intrusion Detection Systems and Flow/Network Analysis products. While such defenses are necessary, they are insufficient for defense in the current threat landscape.
Endpoint detection is a technology that is rising fast to meet the challenge of defending against today’s threats.[su_box title=”About A.N. Ananth” style=”noise” box_color=”#336588″] As the co-founder and CEO of EventTracker, A.N. Ananth was one of the original architects of the EventTracker product, an enterprise log management solution. With an extensive background in product development and operations for telecom network management, he has consulted for many companies on their compliance strategies, audit policies, and automated reporting processes. He is a leading expert in IT compliance, with more than 20 years’ experience in IT-control and operations, and he speaks frequently on these topics. Ananth was involved in product development for various companies including Ciena, Westinghouse Wireless, and Equatorial Communications. He holds an MSEE from the University of Texas and remains active in strategic product direction at EventTracker.[/su_box]
As the co-founder and CEO of EventTracker, A.N. Ananth was one of the original architects of the EventTracker product, an enterprise log management solution. With an extensive background in product development and operations for telecom network management, he has consulted for many companies on their compliance strategies, audit policies, and automated reporting processes. He is a leading expert in IT compliance, with more than 20 years’ experience in IT-control and operations, and he speaks frequently on these topics. Ananth was involved in product development for various companies including Ciena, Westinghouse Wireless, and Equatorial Communications. He holds an MSEE from the University of Texas and remains active in strategic product direction at EventTracker.[/su_box]
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.