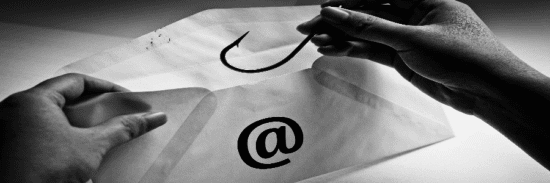
It has been reported that cybercriminals are hijacking legitimate email accounts from more than a dozen universities – including Oxford University, Purdue University, and Stanford University – and using the accounts to bypass detection and trick victims into handing over their email credentials or installing malware. Researchers said in 2020 so far they have discovered a number of malicious campaigns using compromised emails from at least 13 different universities. The highest number of phishing emails detected came from compromised Purdue University accounts (2,068), stolen in campaigns from Jan. to Sept. Behind Purdue University was Oxford (714 phishing emails detected), Hunter College (709), and Worcester Polytechnic Institute (393).
Threat actors have utilized these legitimate emails for different types of attacks. In one, victims received a message from a Stanford University account purporting to be a Microsoft “system message,” which tells users about the status of some quarantined messages. The email offered various links to view the quarantined messages, which, once clicked on, led to a Microsoft Outlook credential-harvesting site or would initiate a malicious code infection. An easy red flag here is that the sender’s email address is a legitimate university account — yet the email purports to come from Microsoft, researchers said.
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.