Security industry insiders are beginning to review and assess the latest PCI Compliance Report published by Verizon. Here to comment on this Report are three expertrs in the field of Information Security: Luther Martin, chief security architect, HP Security Voltage, Andrew Wild, chief information security officer, Lancope and Richard Blech, CEO of Secure Channels.
Luther Martin, chief security architect, HP Security Voltage (formerly Voltage Security):
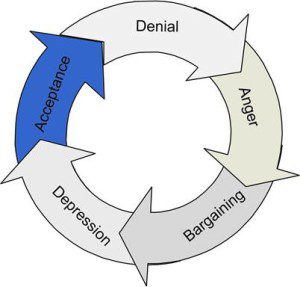
Because all business processes evolve over time, the IT systems that support them also need to evolve over time. When this happens, it’s easy to lose your ability to comply with the PCI DSS, as well as many other data security regulations. The PCI DSS describes a reasonable baseline of controls that everyone should follow. But how these are implemented is really determined by the particular configuration of a particular set of systems. Once those systems evolve, like they have to do to stay useful and relevant, it’s easy to end up with a configuration that isn’t as secure as the previous one. And when this happens, it’s easy to stop complying with the PCI DSS, as well as many other data security regulations. So the data that appears in Verizon’s recent report that suggests that organization are having difficulty maintaining PCI DSS compliance shouldn’t come as a surprise to anyone.
But there are two big steps that can give organizations a better chance of maintaining PCI DSS compliance over time.
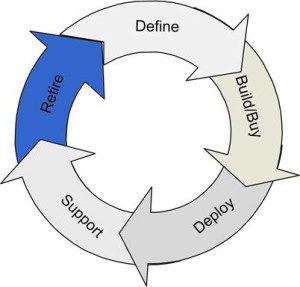
First, organizations should ensure that their IT security staff work closely with the people implementing or maintaining their systems. It’s much easier and cheaper to implement security if it’s done early in the IT system lifecycle. If this isn’t done, adding security later in a system’s lifecycle can be expensive or difficult enough to make IT managers seriously think about whether or not they really want to implement it. But if it’s added early enough, the business case is much easier to make. So the result of considering security sooner rather than later is a much better solution, and one that will do a much better job of protecting your sensitive information. Unfortunately, this isn’t done often enough, which has led people to suggest that the usual system lifecycle model:
Be modified to the following model if security isn’t considered soon enough:
Next, there are architectural issues that can make protecting data much easier. In particular, if the focus is moved from network-centric security to data-centric security, then it’s much easier to handle the evolution of IT systems in a way that doesn’t compromise their security. So instead of trying to make and maintain a strong wall of security between your sensitive data and the hackers outside your systems, just protect your sensitive data, so that even if hackers manage to get it somehow it’s of no value to them. The easiest ways to do this are to either encrypt or tokenize your sensitive information. It’s almost impossible to find and address every security bug in modern IT systems. It’s so hard that it’s reasonable that essentially ALL systems contain exploitable bugs that hackers just haven’t found yet. In this environment, you really can’t rely on your network to protect you from hackers, so a good strategy is to not pretend that your network can protect you. Instead, a better approach is to protect your sensitive data by either encrypting or tokenizing it. If you data is protected by those technologies, the unfortunate fact that your network probably can’t keep out determined hackers really isn’t a fatal flaw. If your sensitive data is encrypted of tokenized, a hacker that manages to penetrate your network will not be able to get any sensitive information, and you’ll be spared the cost and embarrassment of having to deal with a data breach.
Andrew Wild, chief information security officer, Lancope (www.lancope):
As has been said many times over, security is a process, not an end state. IT environments are very dynamic in nature; both security and compliance require very thorough processes to ensure that an organization’s IT environment remains secure and compliant. Many organizations do not have the processes in place to ensure a proactive security posture and are stuck in a reactive mode, constantly trying to keep up.
The fact that post breach investigations have shown that breached organizations were not compliant at the time of the incident is an indication that achieving one hundred percent continual compliance across an entire organization is very challenging. The number of payment breaches in 2014 is more of a testament to the fact that criminal organizations have become very adept at monetizing IT vulnerabilities, using both simple and advanced exploits to gain access to payment card data.
Compliance should be viewed as the minimum requirement, but compliance doesn’t ensure adequate security. Security should be implemented with an approach based upon risk management. Absolute security isn’t likely something that can be achieved, so organizations must prioritize the resources available to implement security based upon an assessment of the risks they face. This has to be an ongoing process, and different organizations will have different risk tolerances and consequently, will have varying levels of security implemented.
I found the four recommendations from Verizon* to be very interesting particularly recommendation #2 “Focus on Scoping.” I agree strongly with the focus on scoping. Organizations must understand their environments, and work to minimize the scope of their payment card environment. However, reducing the scope of the payment card environment can be a difficult task, especially for organizations that haven’t implemented a strong asset management system, and haven’t implemented adequate network segmentation.
* page 7 Verizon PCI Compliance Report
Richard Blech, CEO of Secure Channels (www.securechannels.com):
The dichotomy of the term ‘Best Practices’ – by definition, ‘Best Practices’ does not mean using the broken standard.
The status quo has cybersecurity as an afterthought, cleaning up the mess after the breach. Governance initiatives for many enterprises conjures up a reactive, lackluster, and un-imaginative state of affairs.
PCI-DSS, including other compliance efforts, is dealt with minimal motivation and a ‘getting it over with’ attitude. The substantial finding from Verizon is to be expected as the first step in adopting compliance is a call to action for the people supporting these enterprises. Recent impact to revenue, reputation, and resources for many high-profile organizations has motivated technology leaders to emphasize governance. It is time for the leaders of the technology cyber industry to step up, after all isn’t solving problems the very definition of technology?
The reality is that hackers are nimble and unregulated while the regulating bodies are slow and extremely regulated.
What is left? TECHNOLOGY.
The solution needs to be defined, designed, developed and deployed. There’s an absolute and unequivocal relationship. PCI-DSS calls out Best Practice techniques in protecting critical information, with a wide-array of controls for front-end, middle-tier, and back-end platforms. While the PCI framework is not the cure for all breaches, it was created as a launch pad to first set up an intermediate technical roadmap; second, to create and energize a forum aligning customers, businesses, and technology; and third, to promote checks and balances for each responsible party, fair to their level of activity.
Free eBook: Two-Factor Authentication Evaluation Guide – Get your copy now.
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.