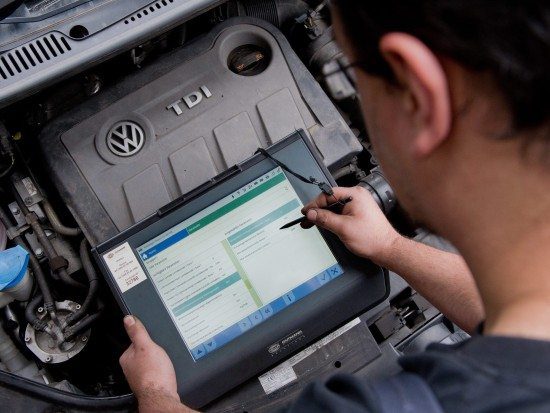
You may have seen news that, following the recent emissions scandal, carmakers seeking approval of new vehicles in Germany will be required to give the country’s regulators access to their software. Paul Farrington, senior solution architect at Veracode have the following comments on it.
[su_note note_color=”#ffffcc” text_color=”#00000″]Paul Farrington, Senior Solution Architect at Veracode :
“The German government should be congratulated for addressing the automotive emissions scandal problem at its core by ensuring that its regulators have full access to carmakers’ code. However, software checks should not be limited to testing for ethical issues such as software-based defeat devices that can cheat regulators. The government must also harness this opportunity to verify that the code in our vehicles meets a minimum standard for security. As connected vehicles become a greater reality across the UK and the rest of Europe, this is not only an opportunity to set a precedent for secure software, but also ensure greater safety for everyone on the road.”[/su_note][su_box title=”About Veracode” style=”noise” box_color=”#336588″] Veracode is a leader in securing web, mobile and third-party applications for the world’s largest global enterprises. By enabling organizations to rapidly identify and remediate application-layer threats before cyberattackers can exploit them, Veracode helps enterprises speed their innovations to market – without compromising security.Veracode’s powerful cloud-based platform, deep security expertise and systematic, policy-based approach provide enterprises with a simpler and more scalable way to reduce application-layer risk across their global software infrastructures.Veracode serves hundreds of customers across a wide range of industries, including nearly one-third of the Fortune 100, three of the top four U.S. commercial banks and more than 20 of Forbes’ 100 Most Valuable Brands.[/su_box]
Veracode is a leader in securing web, mobile and third-party applications for the world’s largest global enterprises. By enabling organizations to rapidly identify and remediate application-layer threats before cyberattackers can exploit them, Veracode helps enterprises speed their innovations to market – without compromising security.Veracode’s powerful cloud-based platform, deep security expertise and systematic, policy-based approach provide enterprises with a simpler and more scalable way to reduce application-layer risk across their global software infrastructures.Veracode serves hundreds of customers across a wide range of industries, including nearly one-third of the Fortune 100, three of the top four U.S. commercial banks and more than 20 of Forbes’ 100 Most Valuable Brands.[/su_box]
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.