Snapchat, eBay, JP Morgan, Sony Pictures and even the White House. The widespread data breaches over the past few years confirms the fact that even large multinational companies and government organisations with huge security budgets are unable to completely defend themselves against the latest threats and smartest cyber criminals. Offenders can obtain data they are looking for by targeting their attacks and increasingly, it seems they are targeting the weakest link of the chain: the user. In most cases this can be stolen credentials, an un-patched desktop or just a careless employee. And once cyber criminals successfully acquire that, they are easily able to exploit the opportunity and steal valuable company data. But how can this happen when companies spend millions of dollars on cyber security?
According to the 2015 Cost of Cyber Crime Study from the Ponemon Institute, deployment of security intelligence systems makes all the difference. Findings in the study suggest companies using security intelligence technologies were more efficient in detecting and containing cyber attacks. As a result, these companies enjoyed an average cost savings of $1.9 million in 2015 when compared to companies not deploying security intelligence technologies and experienced a substantially higher ROI (at 23 percent) than all other technology categories presented.
With these statistics in mind, we would presume that companies would focus on these kind of IT security solutions. But the Ponemon report suggests otherwise; in fact, according to the report, activities relating to IT security in the network layer receive the highest budget allocation. Companies tend to stick to the traditional approach of IT security and defend their perimeter with the most effective control-based solutions.
However, this old, dictatorial approach is not efficient anymore in securing the corporate environment and it is now crucial to include users within this perimeter. Malicious insiders and external attackers who acquired valid user credentials hold an advantage over a company’s primary security tools, because these tools are designed to protect against external threats, not against trusted employees.
But what can companies do if they really want to fight against the latest threats?
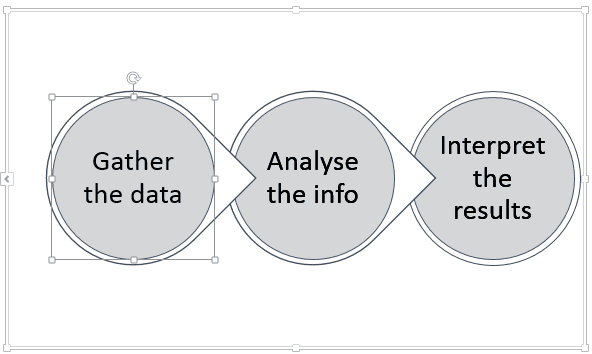
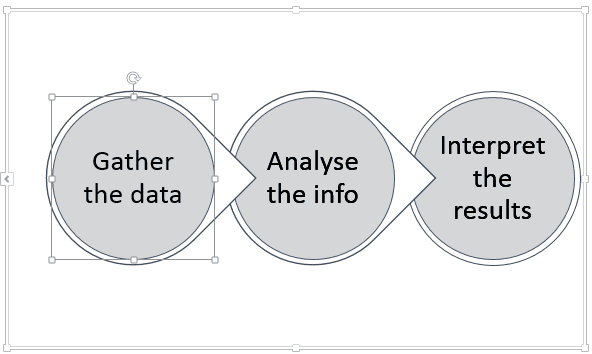
- Firstly, they must create a balance between controlling and monitoring IT security solutions. Traditional control-based solutions are unable to prevent all data breaches, as these are mainly designed against known threats. Since more and more “unknown unknown” threats menaces companies, they must create a balance by introducing machine learning based monitoring security solutions. High quality monitoring tools, such as user behaviour analytics or network forensics solutions are able to detect unknown threats and alert the security team to initiate an immediate action.
- Secondly, they must properly analyse the data generated in the monitoring process. The analysis of this data would have required serious resources even several years ago but since then, the arrival of machine learning algorithms in various big data security analytics tools has simplified the process significantly. Machine learning solutions are able to reveal the trends and patterns behind the data with a good approximation, saving a lot of time for security analysts, who are continuously searching for signs of potential data breaches.
- Thirdly, it is crucial to find the ideal balance between the use of automated responses and experienced security specialists – both of them have a real value in the IT security infrastructure. One of the main reasons for using security analytics solutions is to relieve the heavily overloaded security experts. There are a lot of tasks which can be easily automated, such as the analysis of simple network and user data, e.g. login-logout times or location. But when machine learning algorithms find an anomaly or deviation, the well-trained security experts are also needed. They must analyse simple security alerts to identify actual attacks to determine the root cause of problems and to start the required counter measures such as disabling the user account.
[su_box title=”About BalaBit” style=”noise” box_color=”#336588″]

Balabit’s Contextual Security Intelligence™ Suite protects organizations in real-time from threats posed by the misuse of high risk and privileged accounts. Solutions include reliable system and application Log Management with context enriched data ingestion, Privileged User Monitoring and User Behaviour Analytics. Together they can identify unusual user activities and provide deep visibility into potential threats. Working in conjunction with existing control-based strategies Balabit enables a flexible and people-centric approach to improve security without adding additional barriers to business practices.
Founded in 2000 Balabit has a proven track record including 23 Fortune 100 customers amongst over 1,000,000 corporate users worldwide.[/su_box]



