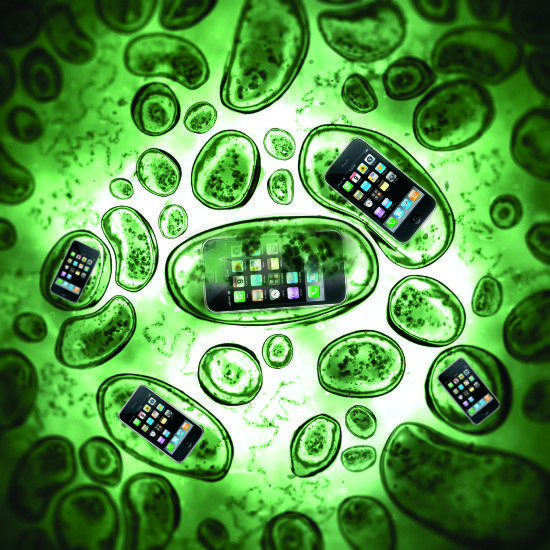
Mobile technology has fast become a part of daily life for many firms. As more and more companies integrate smartphones and tablets into their processes, it is natural to worry about how viruses are targeting these devices and to try to understand why information security jobs are a key growth area.
A background to mobile device viruses
The very first viruses that targeted smartphones did not make news headlines largely because of the relatively small uptake for the devices, thus limiting the impact. However, as demand and access has risen, so too has the threat to users.
Featured Download: Social media access at work. Do your employees know the rules?
Compounded by an increase in the connectivity and capability of these devices, the impact any attack will have has the potential to be truly devastating. It is still at a relatively low level in comparison to attacks on PCs and laptops, but it is nonetheless increasing.
New developments for mobile and tablet attacks
Driving the new wave of viruses on tablets and smartphones is, naturally enough, cash. The designers, or authors, of such malware can now make significant profits from their work. With more banking and shopping transactions completed online, this is easy to understand.
To put it into perspective, from 2010 to 2011, cyber security industry reports saw a 93% increase in the number of vulnerabilities to mobile devices.
Delivering the viruses
The most common form of malicious coding targeting tablets and smartphones is a Trojan. To all intents and purposes, these can look like regular pieces of mobile software and are installed on a device as any commonly accessed app would be.
A further option for virus authors is to modify the code of popular apps delivered to a person’s mobile device in the same way upon purchase and download.
How the viruses attack
Once a user has installed the virus on their tablet, smartphone or ‘phablet,’ there are a number of ways in which the virus can attack.
One of the most common is to collect personal data held on the device. This can include information about the operating system, the phone set up, and its IMEI data such as contacts. Collecting personal information allows the attackers to track how the device is used and where and to steal media files, such as images, video files, and sensitive corporate data.
Further from this are financial Trojans, which monitor transactions made using the device, stealing card information, key stroke data, passwords and, through this, accessing otherwise secure accounts.
A rising tide
Finding individual vulnerabilities of devices is the key to most successful virus attacks. Unfortunately, with the use of smartphones and other mobile devices on the rise, the range of vulnerabilities to be exploited is increasing. Further, as the number of operating systems on the market grows, there is an even greater number of potential weaknesses.
These weaknesses are being tackled head on by ‘white hat’ hackers and security professionals. Additionally, every individual user of a company device has his or her own responsibilities. Ensuring all anti-virus systems are up to date is crucial, as is ensuring that all wireless access points are secure and that all downloads and installations come from trusted sources.
About Acumin
 Acumin is an international Information Security and Information Risk Management recruitment specialist. The company works with a variety of markets comprising of End Users, IT Security Vendors, Systems Integrators and Consultancies.
Acumin is an international Information Security and Information Risk Management recruitment specialist. The company works with a variety of markets comprising of End Users, IT Security Vendors, Systems Integrators and Consultancies.
Acumin provides a range of specialist services which include contingency Permanent Recruitment, Contract Recruitment and retained Executive Search. For SMB and Enterprise End User clients, Acumin facilitates the development of internal Information Security and Risk Management teams across the UK, Europe and United States.
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.