Previously only available to nation-states, it’s no secret that ransomware is now affecting everyone from consumers to hospitals to enterprises. In honor of National Cybersecurity Awareness Month, I have pulled together a comprehensive overview on the threat, based on my years of studying cyberwar—plus new findings from the Comodo Threat Research Labs. It’s time to arm you with the knowledge you need to recognize and prevent these attack methods from affecting you or your business.
What is Ransomware?
Ransomware is a “cryptovirology” attack. It can devastate individuals and organizations by locking up or encrypting their proprietary data in a denial-of-access operation. Attackers demand a payment in exchange for renewed use or decryption.
This is a form of extortion. In the past, some types of ransomware were merely “scareware” in which the attacker would fraudulently claim to be law enforcement and demand a payment, but today many strains of ransomware in fact use powerful encryption.
Computer users are targeted via email and malicious attachment, or drive-by download of an infected website. Increasingly, ransomware is installed via traditional hacking methods. Often, social engineering is used, as attackers tempt users with attractive information including tainted hyperlinks, taking advantage of prior target reconnaissance to deliver a powerful attack. Through any of these methods, the attacker can deliver trojan horse malware that possesses a strong encryption capability.
The primary targets of many ransomware operations are organizations. For example, hospitals simply cannot work without their data, which makes them a good target for attack and a likely payer of ransom. There have already been millions of successful attacks, and in the future – because everything that is “smart” is hackable – it is possible that appliances such as smart TVs and refrigerators could be held hostage to cyber criminals.
The cost of a good ransomware package can be around $5,000, but the software can earn as much as $25,000 per day in income. The payment scheme needs to be hard to trace. The attackers are often able, through wire transfers, premium-rate text messages, pre-paid voucher services, Tor hidden services and bitcoin, to achieve a high degree of anonymity for their operations. Finally, dark web vendors have begun to offer ransomware a service.
History of Ransomware
The ransomware concept has been around since at least 1989, when Joseph Popp used the “AIDS” malware to hide files and encrypt their names, demanding victims pay $189 to the “PC Cyborg Corporation” to get their data back.
A major step forward came in 1996 when an IEEE paper explained how public key encryption could be used to carry out a “cryptoviral” extortion attack in which the attacker creates a key pair and places the public key in the malware, and retains the private key.
However, fifteen years later, in 2010, WinLock was still using older methods, such as blocking access to the operating system by displaying pornographic images and then requesting victims to send a $10 SMS in exchange for a code that would unlock their computers. This sounds like a trivial hack, but cyber criminals made millions in profits.
In 2011, another type of ransomware claimed to be a Windows Product Activation notice, telling users that they had been a “victim of fraud” and requesting that a “free” but, in reality, quite expensive international telephone number be called for remediation.
Citadel / Zeus
In 2012, Reveton, or the “Police Trojan,” displayed a warning that the victim computer was being used for criminal activity such as child pornography, and demanded that the user pay a fine with an online prepaid cash service. This malware would display the computer’s IP address and pictures of the victim from the computer’s webcam as a way to scare the victim into action.
Ransomware now uses highly sophisticated encryption schemes, which are nearly impossible to crack without the private key.
In 2013, CryptoLocker used a 2048-bit RSA key pair, informing the victim that the private key would be deleted if a Bitcoin or a pre-paid cash payment was not made within 3 days. One variant, CryptoLocker.F, required users to visit a web page and enter a CAPTCHA code so that automated processes could not scan the malicious payload.
In 2014, the U.S. Department of Justice targeted CryptoLocker as part of Operation Tovar, isolating the Gameover ZeuS botnet, which had earned millions in ransom, and issued an indictment against Russian hacker Evgeniy Bogachev.
In 2014, CryptoWall used a malvertising campaign on the Zedo ad network on several major websites. The ads redirected the user to rogue websites and used browser plugin exploits to download the payload. The payload also signed with a digital signature in order to appear trustworthy. Another version written in JavaScript in an email attachment downloaded executables disguised as JPEG images. It also created new instances of explorer.exe and svchost.exe to communicate with its servers. FBI: criminals earned at least $18 million.
2016: Locky, delivered by email, allegedly an invoice requiring payment, with an attached Microsoft Word document that contains malicious macros. When opened, the document appears to be full of garbage, and asks the user to “Enable macro if data encoding is incorrect,” or a social engineering trick. If yes, the user will run a binary file that downloads a Trojan that encrypts files matching particular extensions. They then have a .locky file extension. Then the user must download the Tor browser and visit the hacker’s’ link for further information, where the hacker will ask for a 0.5 to 1 bitcoin payment. Hospitals have been victims.
2015: ransomware delivered via hacking such as Linux-based web servers.
Ransomware Cryptography
As with all software, ransomware has varying levels of sophistication. Simple “lockers” have evolved to highly professional encryption, using solid public-key cryptography. Ransomware may not only encrypt your files, but your hard drives as well. Further, it can search for vulnerable network shares, and file backups.
Monetary payment is typically the attacker’s goal. In exchange, the attacker will provide the victim with a program that can decrypt the files, or send an unlock code to undo the payload’s changes. Some companies are thought to have Bitcoin as part of their contingency planning.
The attacker will retain the decryption key until the victim renders an extortion payment. The victim can then send an asymmetric ciphertext to the attacker, which the attacker will decipher, and then the attacker will provide the required symmetric key for decryption.
The victim must be careful with payment, however, as the attacker may also have managed to create a backdoor in the victim’s computer that will allow for follow-on attacks.
Comodo Ransomware Analysis
Comodo has access to a wide data set. Out of 253 Country Code domains, Comodo has seen ransomware infections in 206 country domains.
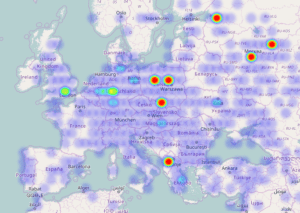 Russia
Russia
Only accounting for locations where we possess significant visibility, the Comodo top ten sites are:
- Albania
- South Korea
- Thailand
- Indonesia
- Malaysia
- Australia
- Russia
- Latvia
- Philippines
- South Africa
Ransomware Defense
All hope is not lost! There are many things you can do to proactively prevent and reactively respond to a ransomware infection. First things first: awareness of the problem, along with training in social engineering and fostering a suspicion of hyperlinks and email attachments.
At the sysadmin level, macros and embedded code should be minimized. It is also a good idea to whitelist applications. Anti-virus should be installed, software patched, and the principle of “least privilege” enforced throughout the network.
In one case, one ransomware victim wound up infecting 500,000 files that he had access through network shares.
It is critically important to backup all data offline, not via network shares or a connected network share. The attacker will find and encrypt those too!
For reactive mitigation, enterprises should develop a range of contingency plans for business continuity and realize that for sophisticated ransomware, recovery may not be possible.
The FBI discourages the payment of extortion demands, as it will not guarantee anything.
[su_box title=”About Kenneth Geers” style=”noise” box_color=”#336588″][short_info id=’94167′ desc=”true” all=”false”][/su_box]
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


