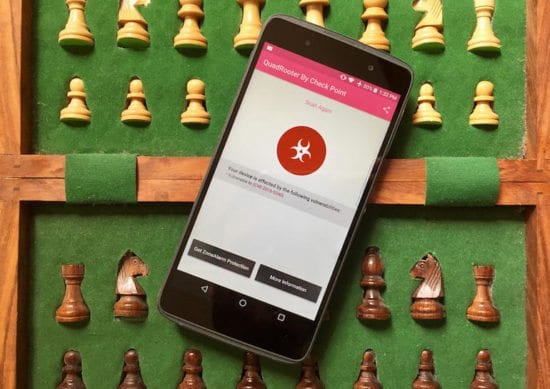
A series of vulnerabilities were found that would allow an attacker to gain full control of an Android device that is manufactured with a Qualcomm chip, known as the Quadrooter flaws. Black Duck discusses this flaw and the challenge that users face in protecting their code throughout the supply chain. Mike Pittenger, VP of Security Strategy, Black Duck commented below.
Mike Pittenger, VP of Security Strategy at Black Duck:
 “ This illustrates the challenge organizations and individual users face in their supply chains. Each device includes code from multiple suppliers, and even when the vulnerabilities are addressed by the responsible vendor or community, it still has to work its way to the end devices. Some vendors will update promptly, while others may not be able to react as quickly. The final step is updating the users’ phones. While automatic updates work well, many users will ignore repeated requests to update, leaving their devices vulnerable. Many times attackers are simply looking for a foothold as a first step in a breach. They can use this initial device to continue their attack by pivoting to other devices.
“ This illustrates the challenge organizations and individual users face in their supply chains. Each device includes code from multiple suppliers, and even when the vulnerabilities are addressed by the responsible vendor or community, it still has to work its way to the end devices. Some vendors will update promptly, while others may not be able to react as quickly. The final step is updating the users’ phones. While automatic updates work well, many users will ignore repeated requests to update, leaving their devices vulnerable. Many times attackers are simply looking for a foothold as a first step in a breach. They can use this initial device to continue their attack by pivoting to other devices.
It is more critical than ever that organizations understand what is running in their environments. While BYOD policies and network partitioning can address issues with mobile devices, there are hundreds and thousands of other devices running proprietary, 3rd party and open source code that can contain vulnerabilities as well. Regulatory standards including HIPAA, HITRUST, and NIST all require patching of known vulnerabilities. What organizations sometimes forget is that this includes vulnerabilities in their own code.”
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.