The Internet of Things includes both traditional electronics and everyday “things” embedded with sensors, computing, and networking capabilities.
- Coffee Makers
- Thermostats
- Refrigerators
- Cars
- Even Cows: wireless sensors tell farmers when cows get sick or pregnant, transmitting 200 MB per cow a year
Even now the Internet of things is all around us:
Connected homes:
- Smart thermostats
- Smart Appliances
- HVAC systems
- Security
- Smart Lighting
- Entertainment Systems
- Risks: Intrusion of privacy, risk to your physical home
Wearables:
- Fitness bands
- Smart Watches
- Smart Glasses
- Action Cameras
- Risks: Financial Information, Location
Industrial Internet:
- Real-time analytics
- Factory automation
- Robotics
- Supply Chain Efficiency
- Risks: Financial Information, trade secrets
Connected Cities:
- Smart Meter Technology
- Smart Traffic Lights
- Smart Parking Meters
- Electric Vehicle Parking
- Real-time analytics
- Risks: Safety, Financial Information, Location
Connected Cars:
- Safety
- Vehicle Diagnostics
- Information and Navigation
- Fleet Management
- Risks: Safety, location
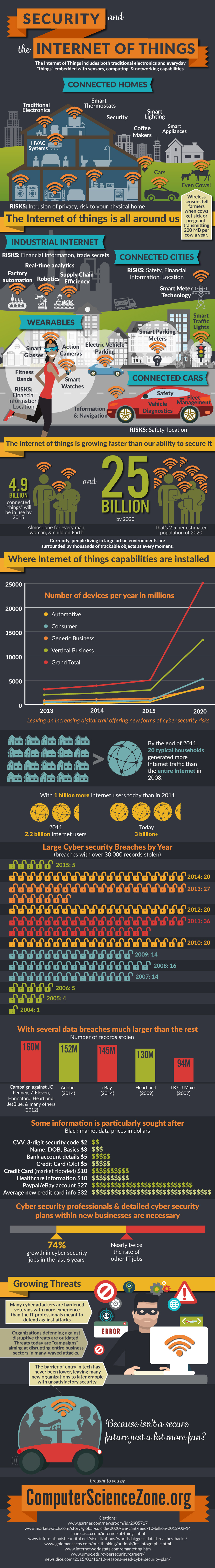
The Internet of things is growing faster than our ability to secure it:
- 4.9 billion connected “things” will be in use by 2015
- Almost one for every man, woman, and child on Earth
- And 25 billion by 2020
- 2.5 per estimated population of 2020[2]
Currently, people living in large urban environments are surrounded by thousands of trackable objects at every moment.
Leaving an increasing digital trail offering new forms of cyber security risks…
By the end of 2011 20 typical households generated more Internet traffic than the entire Internet in 2008.[3] With 1 billion more Internet users today than in 2011.[6] (2011 2.2 billion Internet users, today 3 billion+)
Large Cyber security Breaches by Year:
(breaches with over 30,000 records stolen)[4]
2015: 5 so far…
2014: 20
2013: 27
2012: 20
2011: 36
2010: 20
2009: 14
2008: 16
2007: 14
2006: 5
2005: 4
2004: 1
With several data breaches much larger than the rest.
And some information is particularly sought after.
Cyber security professionals, and detailed cyber security plans within new businesses are necessary.
74% growth in cyber security jobs in the last 6 years[7] Nearly twice the rate of other IT jobs
Growing Threats:
Many cyber attackers are hardened veterans with more experience than the IT professionals meant to defend against attacks.
Organizations defending against disruptive threats are outdated. Threats today are “campaigns” aiming at disrupting entire business sectors in many-waved attacks.
The barrier of entry in tech has never been lower, leaving many new organizations to later grapple with unsatisfactory security.
Because isn’t a secure future just a lot more fun?
Source: ComputerScienceZone.org
Citations:
- http://www.marketwatch.com/story/global-suicide-2020-we-cant-feed-10-billion-2012-02-14
- http://www.informationisbeautiful.net/visualizations/worlds-biggest-data-breaches-hacks/
- http://news.dice.com/2015/02/16/10-reasons-need-cybersecurity-plan/
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.