At this point, everybody knows phishing is a threat.
But then, it’s difficult to deny. As Verizon points out, over 90 percent of data breaches include a phishing or social engineering component, including many of the high profile breaches we all read about each week.
In fact, from a security perspective, phishing is the single greatest threat to most organizations, whether they’re tiny family owned businesses or huge multinational conglomerates.
So, what are most organizations doing to defend against phishing?
Naturally, they’re… doing almost nothing. Best case, they might be holding an annual awareness session in some dark basement room, where a bored intern tries to explain why everybody should stop clicking on dodgy links and attachments.
Now yes, most organizations have implemented some sensible technical controls, such as advanced spam filters and blacklists. They might even go a stage further, by implementing content filtering technologies, and email authentication protocols such as DMARC, SPF, or DKIM.
But the truth is no matter how good your technical controls are, some phishing emails will always reach your users’ inboxes. And when that happens, substandard awareness training won’t be enough to prepare them.
A Spotter’s Guide to Phishing Lures
One of the biggest issues with simply telling users to “watch out for suspicious emails” is that threat actors use a wide range of sophisticated tactics to fool their victims. An individual user might be adept at identifying potentially malicious attachments, but that’s nowhere near enough to ensure the security of your organization.
To give you a feel for the sorts of emails your users will need to be able to identify, here’s a quick rundown of some of the most popular phishing tactics:
- Credential theft
Historically one of the most popular phishing tactics, threat actors will typically use so-called phish kits to construct convincing replicas of legitimate service sites, such as PayPal, Google Drive, or Facebook. Once this is done, they’ll send out generic phishing lures, asking would-be victims to re-enter their login credentials in order to continue using the service in question.
Once credentials have been successfully harvested, threat actors will look to steal money directly, reuse the credentials on other sites in search of profits, or sell the credentials via an underground market.
2) Malicious attachments
Malicious attachments have always been a part of the phishing world, and are still successfully transmitting all sorts of malware each year. From ransomware and spyware installers to high tech worms, there’s no telling what will be coming next. And with more and more malware strains incorporating self-propagating functionality, the potential dangers of malware-laden phishing attacks is at an all-time high.
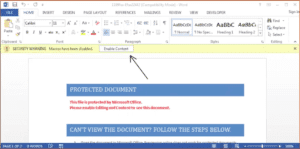
In recent years, many threat actors have utilized in-built Visual Basic macro functionality in Microsoft Office applications as a delivery mechanism for malicious code. These malicious Office documents are often disguised as invoices or business proposals and attached to seemingly plausible lures, making them difficult for the average user to identify.
Once opened, malicious Office documents often advise users to enable macro content.
3) Drive-By Downloads
While malicious applications play a significant role in the world of phishing, they don’t always come in the form of attachments. Similar to credential theft scams, some threat actors prefer to direct their victims to a custom-built phishing site in order to spring their trap.
In some cases, these sites are designed to appear legitimate, and appear to offer valuable software such as antivirus applications or new patches. Others initiate downloads automatically, and attempt to abuse autorun functions built into popular operating systems.
While both approaches have their pro
s and cons, they both effectively circumvent popular technical controls designed to scan and identify malicious attachments.
Above is a real phishing lure used to distribute the Locky ransomware trojan
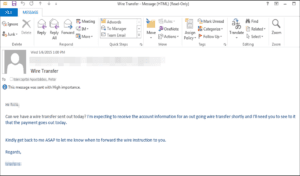
4) Business Email Compromise (BEC) or CEO Scams
Perhaps the most audacious of all phishing emails, BEC scams involve spoofing the email address of a senior executive within a target organization, and simply asking members of the payments team to wire a large payment quickly.
That’s it.
Now you might be thinking nobody would ever fall for that, but unfortunately, you’d be wrong. According to the FBI, this type of phishing scam has cost businesses all over the world over three billion dollars since 2013.
And in fairness, it’s not too difficult to understand why. Entry level payments staff don’t typically receive emails directly from senior executives, and in many cases these scam emails really do appear to come directly from those executives. Often, if payment isn’t made immediately, follow up emails are sent to reiterate the “importance” of the matter.
5) Holiday Themed Attacks
If you’re a reasonably security conscious person, it can sometimes be difficult to understand how other people are so consistently fooled by phishing emails. After all, how hard can it be to identify a malicious email?

But what you may not realize is that phishing threat actors are surprisingly good at developing convincing lures, and they have plenty of tricks up their sleeve. Holiday themed phishing campaigns, like the one below, consistently trick a far greater percentage of average users than generic alternatives.
6) Spear Phishing
Holiday themed attacks might seem sneaky, but they’re little league stuff compared to some of the advanced spear phishing campaigns we’ve observed. Spear phishing emails are highly targeted, often designed for just one specific recipient, and at their worst can include highly specific details of ongoing projects.
We have, for instance, observed cases where threat actors had conducted attacks on mid-sized contracting firms purely to obtain information that could be used to inform phishing attacks on their larger partner organizations. Even with high quality training these attacks can be difficult to identify, so the average executive or senior manager has next to no chance.
Do, or Do Not… There is no “Try”
Of course, the attacks described above are just a small selection of the tactics used every day by coordinated threat actor groups. Cybercrime has become a highly evolved industry, and the most sophisticated threat actors routinely capitalize on every available event, relationship, and political climate to produce highly evolved phishing campaigns.
In case you’re wondering, even nation state-operated and sponsored hacking groups make regular use of spear phishing to initiate their activities. How do you fancy your chances of identifying a spear phishing campaign constructed by the CIA, or corresponding groups in Russia, China, or North Korea?
OK, so maybe phishing emails aren’t so easy to spot after all. But what’s the point? How does this help us develop better training programs?
Well, the first thing it does is completely dispel the idea that we can train users once per year, ask them to watch out for phishing emails, and leave it at that. If that’s all we can manage, we might as well not bother, because it won’t change anything.
Instead, what we need is a program that really walks the walk, and to do that we must have an objective means of examining progress. After all, how can we possibly know if our users are getting better at spotting phishing emails unless we test them?
And the simple truth is that there is only one way to do it: Phish your own users… regularly.
Yes, you read that correctly. In order to train your users to identify and report phishing emails, you must construct and send out your own simulated phishing campaigns, and track your users’ responses.
Naturally, you’ll need to provide some training first, but perhaps not as much as you might think. An initial training session, which would outline how the program will work and cover some of the most common phishing themes, might only take an hour or two. From there, additional training can be immediately delivered electronically to any user who “fails” one of your phishing simulations.
Not only will this process tell you unequivocally how good your users are at identifying phishing campaigns, and enable you to track their progress, it also enables more competent users to avoid wasting their time on training they don’t need. Gradually, as your campaigns become more sophisticated, more users will start failing, and thus will start receiving online training.
Easy, right?
Phishing Practice
As you might have already guessed, implementing a program like the one described above is a little more complicated than it sounds… but not too much. In essence, there are four key components to a powerful phishing defense program:
- Real world experience
If you’re going to go down this route, “winging it” isn’t an option. In order to consistently develop realistic phishing campaigns, you’ll need a constant supply of real-world phishing campaigns to base them on, along with intelligence on the latest phishing trends and tactics.
- An easy reporting system
In the fight against phishing, we don’t just want our users to ignore or delete malicious emails. What we really want is for them to report those emails to us promptly, so they can be used to inform future campaigns, training materials, and technical controls such as spam and content filters. To that end, it’s vital that the reporting process be made as easy as possible for your users.
In my experience, the single best way to do this is to add a simple “Report Phish” button directly to your users’ email client. That way, as soon as their suspicious are aroused, they can hit one button to send it straight to your security experts.
- High quality training materials
It should go without saying that high quality training materials are an essential element of any security training program. In this case, you have the opportunity to deliver powerful and tightly focused training material at precisely the moment it’s needed… so don’t cut corners.
Multimedia training pages are consistently more impactful than those relying on a single medium, so try to include text, video, audio, graphics, and anything else you feel might aid in the transmission and retention of vital information.
- Executive buy-in
This approach to phishing defense is absolutely not a “quick fix.”
Yes, you’ll start to see substantial improvements in your workforce very quickly, and yes, that will have a strong positive impact on your organization’s security profile. But equally, if you take the program away, within a few months you’ll be right back where you started.
And persuading budget holders to fork out additional money for training likely won’t be easy. You’ll need to develop a compelling business case, using current expenditure on incident response and related fields to evidence the need for a phishing specific program. Once the program is established, you’ll need to identify and track relevant metrics in order to prove a continued need for funding and investment.
Executive buy-in is essential to the success of this type of program, and quite simply you’ll need to do everything you can to keep budget holders on-side, as without their support your program simply will not last.
The Hard Truth
At this point, you’re probably thinking this approach is going to require a lot more effort and investment than the program you currently have in place.
And you know what? It will.
But here’s the thing. The program you have in place is poor. It isn’t keeping your organization safe from phishing, which as we’ve already seen accounts for a huge proportion of incoming attacks.
So yes, implementing a program that actually does make your organization more secure will mean investing more resources, whether you develop the program entirely in-house or if you select a vendor to do it for you.
But, thankfully, there is a payoff.
Security incidents are a hugely costly occurrence for most organizations, and data breaches even more so. If you implement a program that genuinely improves the ability of your users to identify and report phishing emails, you’ll be dramatically enhancing the security profile of your organization.
That means fewer security incidents, fewer data breaches, and overall a lot less expenditure on incident response, not to mention fines and compensation. And in all my years of designing and implementing programs like the one I’ve described here, I’ve never seen a case where the initial investment outweighed these ongoing savings.
If that isn’t enough to persuade you, I don’t know what will.
[su_box title=”About Dane Boyd” style=”noise” box_color=”#336588″][short_info id=’102569′ desc=”true” all=”false”][/su_box]






