The sad kinetic situation of the Russian war in Ukraine has created much instability on the world stage – observing the fallout of human tragedies and loss of life – facts we are all very much aware of and tuned into from the daily reports from the media. However, there are several unknown unknowns, of which those outside of the world of Cyber, OSINT, and Research may not be unaware of – the members of the unindoctrinated public. But before we can look at the overall logical implications, we may all face as we enter the new era of the New Cold War (NCW), a visit back in the time machine may help set the scene.
Circa summer 1945, as World War II comes to closure a group of Russian Schoolchildren from the Vladimir Lenin All-Union Pioneer Organization 1, a Soviet version of the Boy Scouts, presented the United States Ambassador in Moscow with a gift of a large carved wooden replica of the Great Seal of the United States – as a gesture of friendship to their wartime allies, AKA the United States. The wooden plaque hung in the Ambassadors study at the Spaso House with pride, but unknown to the recipient, this gestured gift also contained a cutting-edge listening device, used by the Soviets to eavesdrop on conversations whenever they wanted. The plaque hung undetected in the ambassador’s study until 1952— a staggering seven years. It would come to be known colloquially as “The Thing.” – See Fig 1.
Fig 1 – The Thing


With a background out of the world of Counterintelligence (CI), it won’t come as a big revelation if I add, for years, and even today I guess, it has been a known known for those on both sides of the fence to casually survey new building constructions of Government buildings – say during a casual dog walk, to get a closer look and feel for where ‘things’ were going – e.g., the power circuits, plugs, risers or other such constructive features which may be of use at some future juncture – maybe say, understanding the layout of a building prior to drilling a hole in the wall, and then rescuing any captives of a terrorist group – for example.
But what do I know about this murky world of Russian Agents – in the mid 1980’s post the Cyprus Seven Trial (also known as the Cyprus Eight Trial) was a Cold War espionage affair uncovered at one of the military bases in Cyprus during 1983 and 1984, I was the very first non-commissioned officer to be put into the pen in a Counterintelligence role – It was a bit like the preverbal pork chop in a … Following that, whilst in Amsterdam in 1993, I was approached by an ex-KGB Agent, a very nice man I am sure – but there is no such thing as anything as ex in the world of Intelligence. I was also lucky enough to spend some time on the ground in the KGB/IRA infested streets of the American Sector of Berlin, so I can attest with first hand awareness, I have smelt (but never tasted) the vodka at close at hand.
The point of above the above introductory paragraphs is to highlight the element of anticipated trust we may or have bestowed on our partners – say taking everything at face value – and here, I feel we may all agree in the new NCW, things must change in the interest of survival.
Some weeks ago, I wrote an article entitled ‘Russian Software Can You Take the Risk?’ – but I feel that outline did not encompass all the areas we must now consider in the new freezing world of technology.
I recall way back when the Government Agency GCHQ were a little more circumspect when it came to trusting technology, only allowing the procurement of laptops and computer systems from the approved list – yet, then a little short sighted as, such systems are of course manufactured with the integration of circuit boards etc from countries such as China!
So, what is the new risk posed by this NCW? Well, no longer do you have to get someone to hang a bugged wooden carving on the wall in your office – all you need to do for maximised invasion, and intelligence gathering is to get them to install a piece software, which at time of install, and even after a diffing process may be reported as clean. However, consider, upon any future updates or patching to that application could, in themselves be carrying an additional payload. And – what if the Russian company I am dealing with have moved to another country, say the USA, surly that would make them a safe and secure bet – maybe! However, whilst they may be out of the direct reach of Putin’s hand, the question is, could they be influenced and put under pressure through any relations left in the Soviet Territory though the well know employment of HUMINT and strong-arm tactics of the FSB?
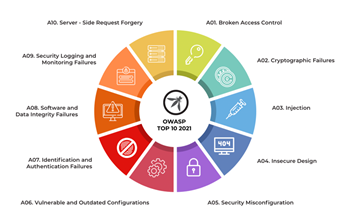
My thoughts here are, is it possible that, notwithstanding the geolocation of a provider of software, they are clean and above board and trustworthy, and out of the pressured reach of the Kremlin? Or could they be sleeping agents of a longer game through which Digital Stealth Infiltration will be empowered at a time which meets the overall objective of the controlling masters? See Fig 2:
Fig 2 – OWASP Outline of potential implementable vulnerabilities
The final decision must of course be left with the owner company, or individual owner of the assets. Are we to throw caution to the wind, and allow our system/systems to be loaded with applications and technologies which could be acting Russian Digital Sleeping Agents? Or are we going to consider the Long Game when it comes to understanding the manifestations of the NCW, and the potentials of Logical Payload vectors sleeping within our assets!
My personal conclusion here is, it is easy to take down a wooden ornament from the wall when you discover it has been infiltrating your space and communicating intelligence to an adversary. It is quite another thing to back out trojan laden, spying software applications from multi-thousands of assets. You decide.
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.



