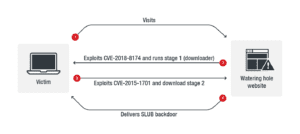
A new watering hole attack is leveraging SLACK, a collaborative platform that lets users create and use their own workspaces, to send command-and-control communications without being detected. The new approach was discovered by Trend Micro.
We can’t paste this image from the Clipboard, but you can save it to your computer and insert it from there.
Expert Comments below:
Usman Rahim, Digital Security & Operations Manager at The Media Trust:
 “Battlefields are increasingly online, and this attack in particular was carefully planned. Watering hole attacks are carried out primarily on specific organizations. Whoever orchestrated this campaign wanted to gather personal and communications information on visitors of a website operated by a nonprofit that supports the North Korean regime. Not surprisingly, the malware strain used has not been seen anywhere else. It also comes as no surprise that the orchestrators chose popular tools that would leave few, if any, traces that would enable anyone to identify them.”
“Battlefields are increasingly online, and this attack in particular was carefully planned. Watering hole attacks are carried out primarily on specific organizations. Whoever orchestrated this campaign wanted to gather personal and communications information on visitors of a website operated by a nonprofit that supports the North Korean regime. Not surprisingly, the malware strain used has not been seen anywhere else. It also comes as no surprise that the orchestrators chose popular tools that would leave few, if any, traces that would enable anyone to identify them.”
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.



