Kevin Bocek, Vice President, Security Strategy & Threat Intelligence at Venafi commented on weaknesses in cryptography used as part of the Open Smart Grid Project (OSGP).
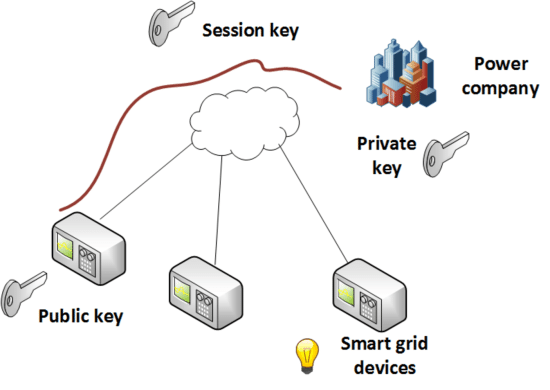
“Weaknesses in cryptography used as part of The Open Smart Grid Project (OSGP) show how fragile the cyber realm is and how technologies we take for granted like encryption, cryptographic keys, and digital certificates can have a very dramatic impact when they fail. Encryption, cryptographic keys, and digital certificates were thought to have solved the Internet’s first real security problems: how do I know I can trust a website or device on the Internet and how do we know we have a private connection? Recently, 54% of UK security professionals surveyed indicated that the system of trust on the Internet was near the breaking point. Whether it’s failed crypto, mismanaged keys, or stolen certificates, it’s clear this is a problem that can’t be taken for granted. We don’t realize it, but trillions of pounds of the world’s economy is built on encryption, cryptographic keys, and digital certificates. And when it breaks, many, many other security controls fail. And with the smart grid, failure is not an option.”
By Kevin Bocek, Vice President, Security Strategy & Threat Intelligence at Venafi
BIO : Kevin Bocek is responsible for security strategy and threat intelligence at Venafi. He brings more than 16 years of experience in IT security with leading security and privacy leaders including RSA Security, Thales, PGP Corporation, IronKey, CipherCloud, nCipher, and Xcert. He is sought after for comment by the world’s leading media such as Wall Street Journal, New York Times, Washington Post, Forbes, Fortune, BBC, Süddeutsche Zeitung, USA Today, Associated Press, Guardian, and Telegraph along with security press including SC Magazine, Dark Reading, and Network World.
About Venafi
Venafi is the market-leading cybersecurity company in Next Generation Trust Protection (NGTP). As a Gartner-recognized Cool Vendor, Venafi delivered the first Trust Protection Platform™ to secure cryptographic keys and digital certificates that every business and government depends on for secure communications, commerce, computing, and mobility. With little to no visibility into how the tens of thousands of keys and certificates in the average enterprise are used, no ability to enforce policy, and no ability to detect or respond to anomalies and increased threats, organizations that blindly trust keys and certificates are at increased risk of costly attacks, data breaches, audit failures, and unplanned outages.
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.