Ransomware’s Early Days
The first documented and purported example of ransomware was the 1989 AIDS Trojan, also known as PS Cyborg. Harvard-trained evolutionary biologist Joseph L. Popp sent 20,000 infected diskettes labeled “AIDS Information – Introductory Diskettes” to attendees of the World Health Organization’s international AIDS conference.
But after 90 reboots, the Trojan hid directories and encrypted the names of the files on the customer’s computer. To regain access, the user would have to send $189 to PC Cyborg Corp. at a post office box in Panama. Dr. Popp was eventually caught but never tried for his scheme as was declared unfit to stand trial. His attorney said he began wearing a cardboard box on his head to protect himself from radiation.
Fast Forward to the Internet Age
With the Internet making it easier to carry out Popp’s ransom idea, cyber criminals began to realize that they could monetise ransomware on a far wider scale.
In 2006, criminal organisations began using more effective asymmetric RSA encryption.
- The Archiveus Trojan encrypted everything in the My Documents directory and required victims to purchase items from an online pharmacy to receive the 30-digit password.
- The GPcode, an encryption Trojan, which initially spread via an email attachment purporting to be a job application, used a 660-bit RSA public key. Two years later, a variant (GPcode.AK) used a 1024-bit RSA key.
The New Wave
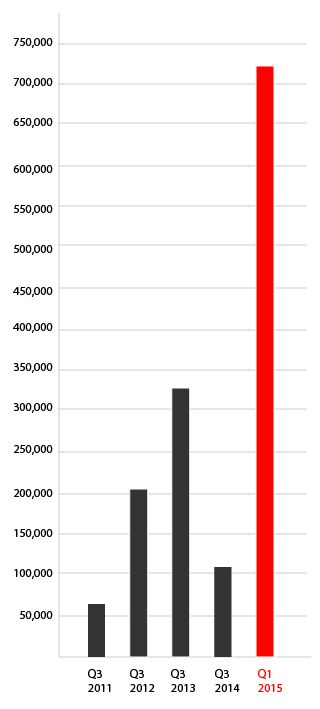
Starting 2011, ransomware moved into big time. About 60,000 new ransomware was detected in Q3 2011, and more than doubled in Q3 2012, to over 200,000. What’s most astounding is that ransomware more than quadrupled from Q3 2014 to Q1. 2015.
 With no signs of slowing down, there are now many, many ransomware variants. Here’s a brief rundown of the ones you should know:
With no signs of slowing down, there are now many, many ransomware variants. Here’s a brief rundown of the ones you should know:
CryptoLocker – first versions appear to have been posted September 2013
- Usually enters the company by email
- If a user clicks on the executable, it starts immediately scanning network drives, renames all the files & folders and encrypts them.
Locker – first copycat software emerged in December 2013
- $150 to get the key, with money being sent to a Perfect Money or QIWI Visa Virtual Card number.
CryptoLocker 2.0 – a new and improved version of CryptoLocker was found in December 2013
- CryptoLocker 2.0 was written using C# while the original was in C++.
- Tor and Bitcoin used for anonymity and 2048-bit encryption.
- The latest variant is not detected by anti-virus or firewall.
CryptorBit – a new ransomware discovered in December 2013
- CryptorBit corrupts the first 1024 bytes of any data file it finds.
- Can bypass Group Policy settings put in place to defend against this type of ransomware infection.
- Social engineering used to get end users to install the ransomware using such devices as a fake flash update or a rogue antivirus product.
- Tor and Bitcoin again used for a ransom payment.
- Also installs crypto-coin mining software that uses the victim’s computer to mine digital currency.
CTB-Locker (Curve-Tor-Bitcoin Locker) – discovered midsummer 2014
- First infections were mainly in Russia. The developers were thought to be from an eastern European country.
SynoLocker – appeared in August 2014
- This one attacked Synology NAS devices. SynoLocker encrypted files one by one.
- Payment was in Bitcoins and again Tor was used for anonymity.
CryptoWall – rebranded from CryptoDefense in April 2014
- Exploited a Java vulnerability.
- Malicious advertisements on domains belonging to Disney, Facebook, The Guardian newspaper and many others led people to sites that were CryptoWall infected and encrypted their drives.
- According to an August 27 report from Dell SecureWorks Counter Threat Unit (CTU): “CTU researchers consider CryptoWall to be the largest and most destructive ransomware threat on the Internet as of this publication, and they expect this threat to continue growing.”
- More than 600,000 systems were infected between mid-March and August 24, with 5.25 billion files being encrypted. 1,683 victims (0.27%) paid a total $1,101,900 in ransom. Nearly 2/3 paid $500, but the amounts ranged from $200 to $10,000.
Cryptoblocker – new ransomware variant emerged in July 2014
- only encrypt files <100MB and will skip anything in Windows or Program Files.
- It uses AES rather than RSA encryption.
OphionLocker – surprise! Another ransomware released during the holidays, December 2014
- ECC (elliptic curve cryptography) public-key encryption.
- 3 days to pay the ransom or the private key will be deleted.
Pclock – greets the New Year, January 2015 by miming CryptoLocker
- Files in a user’s profile are encrypted.
- Volume shadow copies are deleted and disabled.
- 72-hour countdown timer to pay 1 bitcoin in ransom.
CryptoWall 2.0 – ransomware goes on steroids in January 2015
- Delivered via email attachments, malicious pdf files and various exploit kits.
- Encrypts the user’s data, until a ransom is paid for the decryption key.
- Uses TOR to obfuscate the C&C (Command & Control) channel.
- Incorporates anti-vm and anti-emulation checks to hamper identification via sandboxes.
- Has the ability to run 64-bit code directly from its 32-bit dropper. It can switch the processor execution context from 32 bit to 64 bit.
TeslaCrypt – a new CryptoWall variant surfaced in February 2015
- Targets popular video game files such as Call of Duty, MineCraft, World of Warcraft, and Steam.
VaultCrypt – pretended to be customer support in February 2015
- First circulated in Russia.
- Uses Windows batch files and open source GnuPG privacy software for file encryption.
CryptoWall 3.0 – a new version appeared March 2015
- I2P network communication.
- Uses exploit kits to gain privilege escalation on the system.
- Disables many security features on a target system.
CryptoWall 4.0 – 6 months later, in September 2015, a new variant is on the loose
- The most important change from CryptoWall 3.0 to 4.0 is that it re-encrypts filenames of the encrypted files, making it more difficult to decipher which files need to be recovered.
LowLevel04 – this file-encrypting ransomware greeted us in October 2015
- Also known as the Onion Trojan-Ransom
- Spreads via brute force attacks on machines with Remote Desktop or Terminal Services
- Encrypts files using AES encryption but the encryption key itself is RSA encrypted
And finally, a game changer known as Chimera – November 2015
- The hackers will publish the encrypted files on the Internet if the victim doesn’t pay!
[su_box title=”Kieran Laffan, engineer, Varonis” style=”noise” box_color=”#0e0d0d”]  Kieran Laffan, is engineer, at Varonis. Varonis is the leading provider of software solutions for unstructured, human-generated enterprise data. Varonis provides an innovative software platform that allows enterprises to map, analyze, manage and migrate their unstructured data. Varonis specializes in human-generated data, a type of unstructured data that includes an enterprise’s spreadsheets, word processing documents, presentations, audio files, video files, emails, text messages and any other data created by employees. This data often contains an enterprise’s financial information, product plans, strategic initiatives, intellectual property and numerous other forms of vital information. IT and business personnel deploy Varonis software for a variety of use cases, including data governance, data security, archiving, file synchronization, enhanced mobile data accessibility and information collaboration. As of March 31, 2015, Varonis had approximately 3,500 customers, spanning leading firms in the financial services, public, healthcare, industrial, energy & utilities, technology, consumer and retail, education and media & entertainment sectors.[/su_box]
Kieran Laffan, is engineer, at Varonis. Varonis is the leading provider of software solutions for unstructured, human-generated enterprise data. Varonis provides an innovative software platform that allows enterprises to map, analyze, manage and migrate their unstructured data. Varonis specializes in human-generated data, a type of unstructured data that includes an enterprise’s spreadsheets, word processing documents, presentations, audio files, video files, emails, text messages and any other data created by employees. This data often contains an enterprise’s financial information, product plans, strategic initiatives, intellectual property and numerous other forms of vital information. IT and business personnel deploy Varonis software for a variety of use cases, including data governance, data security, archiving, file synchronization, enhanced mobile data accessibility and information collaboration. As of March 31, 2015, Varonis had approximately 3,500 customers, spanning leading firms in the financial services, public, healthcare, industrial, energy & utilities, technology, consumer and retail, education and media & entertainment sectors.[/su_box]
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


