Introduction
This paper will consider the areas surrounding Data Security and look at the multiples of ways in which it may be breached, altered, or compromised, some of which may be obvious, others not so. We will explore this topic based on the security four table legs of CIA+A:
Confidentiality, Integrity, Availability, and Accountability
We will however be concentrating on the areas of Confidentiality and Integrity in relation to the stored data objects (Information). However, at this juncture we must stress that where a mitigation relates to encrypting localised on-board, or attached media, we must keep in mind that this style of security, notwithstanding the media has been secured by encryption, nevertheless, leaves the data objects, and file system exposed to the implication of Availability, as the attached, accessible data objects are still exposed to the imposition of a Ransomware attack.
- Fake Secure Drives: On my global travels, I have encountered several, so-called secure, encrypted drives for sale which are nothing more than a drive sealed within a pin-protected casing. Thus, any security minded users who purchase such a device will be storing their sensitive data assets with the impression they are protected and secured by encryption – when in fact they are open to anyone who may remove the drive from its casing to view the insecure content.
Mitigation: If you care about robust security of your files, only user Certified, trusted, encrypted drives which are built to the FIPS-140/2 Standard.
- Change of Domain Policy: This is a classical mistake, born out of ignorance of the nuts-and-bolts aspects of Digital Security. A Nottingham based Financial Services business were unfortunate enough to be hit with a zero-day computer virus, which spread with some speed within their operational environment. A Major Incident Board was convened, and a team was brought tougher including Senior Members of the IT Security Team, and Directors from the companies Technical Services Board. They concluded that to deploy the style of patch required in the most expedient way would be achieved by changing the Domain Policy to open up access to each of the client systems (Desktops/Laptops), which would be followed up by a quick push of the updated .dat signatures, quickly followed by a reapplication of the required Domain Policy to bring all systems back to their original security posture – all done, and the team stood down. However, it was soon apparent that something had gone wrong when members of the IT Security Team were receiving calls from Ordinary Users reporting that, in one case they could see all files located on the Human Resources Directors local drive, and the calls continued. The issue was, what had not been appreciated by the technical Services Board Director, and the associated Information Security Team was, whilst you may remove the permissions across the domain with the click of a box, to reapply them requires end-system action of a reboot to reinstate the required level of security posture – thus all systems and stored were exposed cross-domain!
Mitigation: 1) Ensure that those in key positions are fully trained and above all competent. 2) Where there is need to take additional steps to secure data (e.g., the HR Director) encrypt the locally stored files. 3) Consider utilising off system, secure, encrypted removable drives to secure sensitive data.
- Trust your Staff: I recall when working for a Local Authority in the East Midlands with an IT Director who could never surprise his staff. He commented to me, ‘no matter what I tell the team at our Town Hall Meetings, they always seem to know before I pass on the information’. That was because they did, as due to poor security, and open folders, some members of the IT Team had full access to the stored data and communications of said IT Director – so yes, they were always aware what was going on!
Mitigation: 1) Ensure that Folders and storage areas are appropriately protected, and not visible to any members of the IT Team (or for that matter any other such unauthorised user). 2) With any sensitive data it is always Best Practice to store such sensitive data-objects off-line, on removable, encrypted storge devices.
- MFD – The forgotten Technology: Some years back I was working as a Consultant for a London based UK Government Agency who worked on sensitive data of the highest classifications. Given their concern over data security, they ran a project to virtualise all desktops/laptops, which were limited to only storing data on servers located within the secured Computer Room. However, they overlooked the fact that on every floor in the building stood an MFD (Multi Functional Device) AKA, a big fat computer, IP addressable, with on-board Print Server, Spooler, Web Server, Hard Drive(s) Storage, that just happens to offer printing facilities, on which the drives were accessible, and of course on this occasion not encrypted, leaving the sensitive data open to both physical and logical abuse!
Mitigation: 1) Always run a Risk Assessment of Data Flows and Storage when engaging such a project. 2) Ensure that where there are configuration options (and there were) apply a level of encryption to the dives to secure any stored data objects. 3) Where Physical Access may be achieved to the on-board drives, always ensure they are physically secure by lock-and-key. 4) When these devices reach end-of-operational life, at the very least ensure the disks are securely overwritten/purged – at best, physically destroyed.
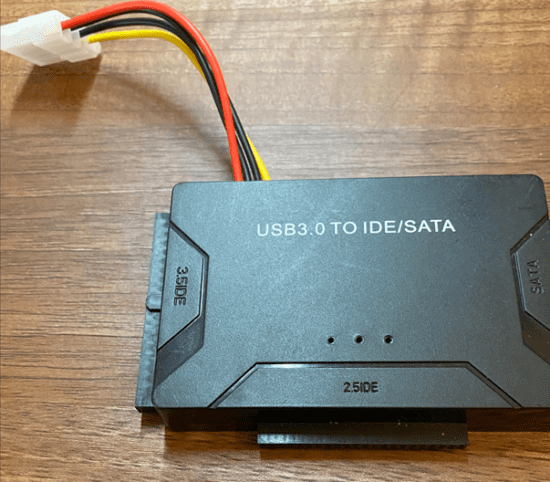
- Trust in Logon Security: Whilst there may be a great faith in the local security associated with say, Windows, or other such Operating Systems, this can be a false sense of security when we consider the security of the data objects stored thereon. Take the average Windows Desktop or Laptop – our user has the full confidence that only they can get to the on-board data objects as they are using a very strong password, along with the associated logon credentials – so all is secure and tucked away from the illicit view of others. However, what our user needs to realise is that, notwithstanding their security credentials, to gain access to the stored data, it is a simple case of physically removing the drive, and then mounting it on to an awaiting laptop via an interface, such as the USB3.0 TO ODE/SATA device as shown at Fig 1 below – from there on, full access to said content may be enjoyed.
FIG 1 – USB3.0 TO ODE/SATA device
Mitigation: 1) Encrypt Local Drives with Bitlocker etc (Keep Keys on USB, or ensure the machine is accommodated with a TPM Chip (Trusted Platform Module). 2) Better still, use a removable, FIPS-140/2 encrypted drive accommodated with some form of additional security mechanisms – say Pin Protected.
- Cloud: If you are using Cloud, and most are in some form or another – ensure that you have completed a full Due Diligence of the Third-Party Supplier, remembering that Cloud, and Third-Party Supply Chains are a known known potential area to introduce insecurity. It would seem here however that, even those who preach good practice such as Experian (https://www.experian.co.uk/assets/data-breach/white-papers/data-breach-supply-chain-risk.pdf) may not be eating their own dog food, as they themselves have suffered another breach, this time involving 24 million accounts, and 800,000 businesses – very worrying! Consider technologies such as AWS S3 Buckets, and ensure they are secured. Cloud environments are one of those areas which can reveal a lot to an OSINT (Open-Source Intelligence) mission which can lead to the acquisition of valuable information.
Mitigation: 1) Consider running your own RED–TEAM activity against any procured, or to be procured service to gain an insight into the overall footprint. 2) Conduct an in-depth review of the service provider at all levels. 3) Once procured and operational, ensure regular service update meetings are held – say every three months. 4) Where valuable logical assets are implicated, consider utilising an Escrow agreement to accommodate security over such assets lodged with the Third Party (Just in case).
- Equipment Disposal: I have seen it so many times, I have forgotten each instance. From disposal of MFD’s, Cell Phones, IoT devices, Printers, Computers, Servers . . . the list goes on. On each of these occasions, these data-holding systems have been disposed of, containing corporate and sensitive data. From Cell Phones which have been allowed to connect to Corporate Systems, to hard drives populated with Local Authority data relating to case files of vulnerable children.
Mitigation: 1) Create and promulgate a Policy/Process to drive the way end-of-life equipment is processed out from the business. 2) Create a register to document the end-of-life journey that all devices take. 3) Hold all such devices in physically secure location until such time they are correctly processed in accord with the mandated Policy/Process.
- Paper: Don’t suffer from Tunnel Vision when securing you data assets – remember, it not just about the digital aspects, but also needs to encompass the other potential carriers of insecurity – e.g., Paper. I recall my very first contract on the South Cost. The Project Manager said to me on my very first day, ‘you need to make a difference and quick to convince the executive we need to look at the company’s overall security posture’. 4 hours later I presented him with a sack full of paper holding client personal details, credit card information, and client bank account details, all of which had been cast out into the general waste bins.
Mitigations: 1) Accommodate the facilities with secure, locked, clearly marked classified waste bins. 2) Produce and promulgate a policy to dive the mandated requirements. 3) Consider using on on-site Secure Paper Shredding/Disposal Service. 4) Educate end users.
- MetaData: MetaData is Data about Data, and can provide much, unintentional information which can range from User Profiling, Departmental Data, Telephone Extensions, right down to IP Addresses and Software Versions. So what! Well just consider the fact that such unintended information can be leveraged to adverse interest to footprint and target an organization, or individual, and can provide a very good launch-point for a Social Engineering attack.
Mitigation: 1) Employ some form of methodology to remove any unwanted MetaData from documents prior to release. 2) May be obvious butensure that documents are not released with the underlying Track Changes embedded – this can be, and has on many occasions be very embarrassing! 3) Consider using secured PDF formats (Locked down, encrypted with password or Certificate).
- DNS: The area of Domain Name System is so often overlooked, and yet is as important to any Penetration Test focused on aspects of IP Addressing. As with some of the aforementioned areas, when inspected under the gaze of an OSINT Methodology, DNS can also produce much intelligence which may be leveraged to attack the organisation. From Zone Transfer, which in one case led to identifying servers with Hard Coded Users ID and Password within scripts, through to the discovery of poor security DNS postures, and other such associated aspects, such as lack of SPF (Sender Policy Framework). DNS Security is a very big area, and one I would encourage you to peruse in the interest of a robust security posture – if that is, you have not already done so. See RFC 4033 URL for more information:
https://datatracker.ietf.org/doc/html/rfc4033
Mitigation: 1) Review your organisations DNS environments – include ~DNS in you Penetration Testing Programmes. 2) Conduct regular security inspections to ensure your DNS environments are secure and serving the required security posture. 3) If not familiar, read RFC 4033.
Conclusion
It may be concluded that the opportunities for Data Compromise exist at multiple levels within the organisation, or with the individual’s interface with technology. When we look toward the multiples of SME’s we can see the area of insecurity manifest by a factor of their overall sum-of-parts in the business sense – from Data Insecurity, to suffering successful Ransomware attacks – this is possibly the group who by volume of numbers are the weakest, and most obvious areas to suffer from some form of insecurity manifesting withing their business worlds.
The case for hardening the overall security posture in multiples of areas is, in my opinion made – maybe a little less box-ticking, and a bit more of getting back-to-basics and understanding the tenants of what nuts-and-bolts security is. In a world which, by the very presence of complex deployments sets the expectation to assure the new age IT/Cyber/Digital Security Professional understands what a robust security posture looks like!







