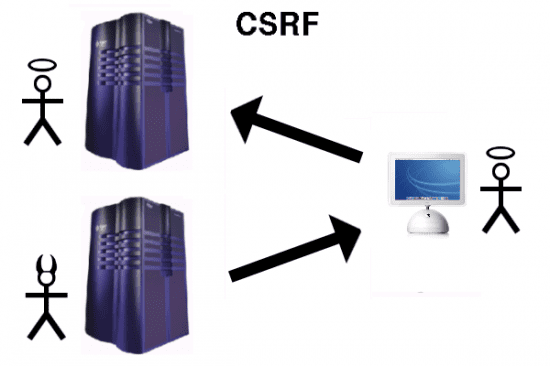
As the security community continues to look for easier ways to mitigate the risk of all-too-common Cross-Site Request Forgery (CSRF) attacks, many within the industry have lamented the difficulties that make it tough to do CSRF token deployment just right. With so many moving parts like, CSRF tokens are frequently used insecurely if at all.
Which is why a pair of researchers from Qualys are now proposing a new header-based browser policy that they say could affect a much simpler, and therefore more broadly effective means of countering CSRF attack techniques.
“There’s nothing particularly wrong with the idea of the CSRF token approach, the problem is people make mistakes,” says Mike Shema, director of engineering for Qualys, who together with his colleague Vaagn Toukharian presented at Black Hat earlier this month a new HTTP header-based policy they call Session Origin Policy (SOS).
SOURCE: darkreading.com
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.