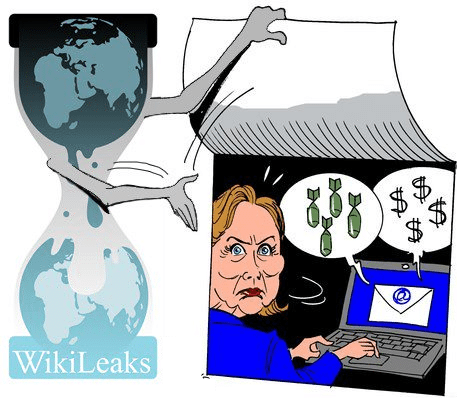
The Democratic National Committee’s email has been hacked and confidential emails have been posted on Wikileaks. The emails outline thoughts on the Bernie Sanders campaign, donors and their backgrounds and entertainers who might be invited or not to the White House. Tim Erlin, Senior Director of IT Security and Risk Management of Tripwire commented below.
Tim Erlin, Senior Director of IT Security and Risk Management at Tripwire:
 “If you’re part of the political process, especially during a hotly contested election, it’s safest to just assume that your emails aren’t private. It’s possible to take measures to protect email contents through encryption, but it takes a fair amount of effort. Few systems are foolproof, and few organizations make the investment to employ consistent encryption. From private servers to hacked email, this presidential election has thrown technology and cybersecurity to the forefront. “
“If you’re part of the political process, especially during a hotly contested election, it’s safest to just assume that your emails aren’t private. It’s possible to take measures to protect email contents through encryption, but it takes a fair amount of effort. Few systems are foolproof, and few organizations make the investment to employ consistent encryption. From private servers to hacked email, this presidential election has thrown technology and cybersecurity to the forefront. “
Lamar Bailey, Senior Director of Security R&D for Tripwire agrees and says, “Emails, texts, messages, pictures, etc. never go away. Anything you put in email, save to your phone or computer can be recovered so use cation. We teach our kids to think about what they are going to say before they speak because you can never take words back. We all need the heed this advice because the same goes for email, texts, and pictures.”
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.