BACKGROUND:
The world’s largest meat supplier, JBS Foods, has been hit by a cyber-attack, the latest in a string of high-profile international hacks which show no sign of slowing down.
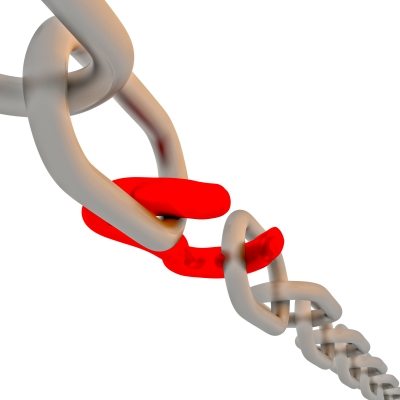
Hackers have been crippling supply chains as a priority, following the Colonial Pipeline attack just weeks ago. Protecting these links between critical systems is vital, as cyber security experts explain below. We can no longer underestimate the supply chain‘s importance or consider its security only as an afterthought. Companies must start protecting it with intelligent cybersecurity.
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.