Should we fear the unknown and uninvited entering our home and business?
Should we block them from access to what we value and are sworn to protect, at least until we can be confident they are not a danger? Do you do this today?
In IT, this is called taking a “default deny security posture,” and while it is strongly recommended by virtually every analyst and expert in the industry, it is only practiced by two groups today:
- A tiny subset of defense, intelligence, and hyper security-conscious organizations
- Businesses and organizations with a mechanism to keep their business moving efficiently while these “unknown” file attachments, scripts, etc. are analyzed and become “known”
The first “safe” group’s staff simply “does without” all unknown files until the analysis on unknowns is complete, delaying for minutes or even hours their access to an attachment or desired application or other file. They ensure security, but pay a price in time and efficiency.
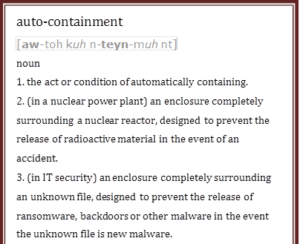
The second safe group utilizes “auto-containment” of unknown files such that they can keep working normally with the file, but are doing so in a safe, “container” until the analysis is completed, and it becomes “known.” The container denies the file access to anyone or anything else while the user can open it and use it with a container-specific version of the needed application, viewer, or other tool.
The third group is likely you (or your organization actually). Your business today chooses to allow the unknown in, before knowing what it is and the things it can do to what you value and are sworn to protect. This is a “default allow security posture,” and there is 100 percent certainty that the third group, including you, is at risk from unknown files.
 How much risk is there? Finding out an hour later that an unknown file allowed in was actually a Trojan, worm, backdoor, or other piece of dangerous malware that has already propagated, self-replicated, sent data back to its master, encrypted/destroyed data, or otherwise delivered its payload is “how much risk.”
How much risk is there? Finding out an hour later that an unknown file allowed in was actually a Trojan, worm, backdoor, or other piece of dangerous malware that has already propagated, self-replicated, sent data back to its master, encrypted/destroyed data, or otherwise delivered its payload is “how much risk.”
In recent weekly update reports from a threat intelligence lab analyzing millions of endpoints, between 5% and 6% of unknown files were ultimately found to be Trojans, worms, viruses, backdoors or other malicious software. Even with the best cybersecurity machine learning algorithms and artificial intelligence scanning available today, some unknown files will not be quickly identified. It is these “unknowns” that your group is choosing to let into your IT infrastructure because your chosen security posture is still “default allow” for unknown files.
This is still a common choice for your peers. It is also common for your peers to be penetrated by malware and to deal with consequences of those infections. If they’re lucky, it just plays out internally with a project to find and eradicate the malware on the machine it first infected and any others it spread to since then. If data was lost or damaged, hopefully a usable backup can be accessed to restore it. If passwords and sensitive data were transmitted out to the attackers, other projects are undertaken to minimize the damage and to close any new “backdoors.” The cost of these infections range from hours of lost productivity to a recent $300 million loss to, of course, fired security administrators, CSOs, CIOs, and others.
If they’re not lucky, they take their turn in the press news cycle as the latest victim, and they apologize and vow to investigate and redouble their efforts to keep their organization and its stakeholders safe.
The evolving 2017 IKARUS Dilapidated Locky ransomware attacks are examples of a hacker organization successfully using the “unknown file” opening to penetrate corporate email systems via newly modified phishing emails with a ransomware payload. Once allowed in via the “default allow” security posture, the phishing emails’ social engineering mimics the office’s scanner/copier or a local vendor to get busy employees to click the attachment and activate the ransomware. These hackers modify their malware every few weeks to stay ahead of virus signature updates and have each new round of ransomware appear as an “unknown.”
Fatih Orhan, head of the Comodo Threat Intelligence Lab said, “The data collected from 85 million endpoints worldwide shows that criminal organizations and other hackers are creating new malware at an astonishing pace; 5-7 percent of the millions of unknown files detected each week are new malware. AV and endpoint protection vendors just can’t keep pace with new signatures for AV and endpoint protection updates, so unknown files are becoming an even bigger threat.”
Choosing to still allow any unknown files into your home or office however, means they are not safe. And neither are you. When it comes to files, applications and other code knocking at your endpoint doors, you should fear the unknown, at least until you understand it. Use “default deny” or “default deny with auto-containment” and simply keep them out until you know.
[su_box title=”About Steven A. Menges” style=”noise” box_color=”#336588″][short_info id=’103583′ desc=”true” all=”false”][/su_box]
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


