The 2014 FIFA World Cup has begun. This month-long tournament brings together the best soccer players in the world to battle for their countries. For the millions of die-hard soccer fans that cannot watch the games on television during typical work hours, many will turn to the internet to find anyway to watch the action as the excitement of the games heightens. The cybercriminal communities are seizing this opportunity to deceive fans online by broadcasting unsolicited advertisements for free live online streaming of the event and fake world cup related promotions that are difficult to resist. This introduces serious security risks and productivity concerns to the enterprise. These are classic baiting techniques that often result into dangerous fraud, phishing and malware attacks.
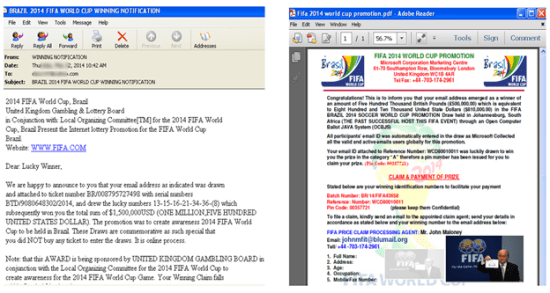
Over the last week, the Dell SonicWALL threats research team has been tracking down all World Cup related spam emails. The emails have a common theme of trying to lure users of providing their personal information in exchange for full access to live streaming videos or to claim prizes from a FIFA lottery. Figure 1 shows one of many phishing email examples being circulated today.
Figure 1: Phishing email example.
For soccer fans inside and outside of the workplace that are looking for free online streaming of the games on their computers, laptops or mobile devices, they’re presented with plenty of bogus sites on the web. Some of these sites will redirect to another URL requiring users to provide their credit card information for full access to live streaming while others will prompt users to download special video playback software or install “missing plugins” that almost assuredly, if users click that URL, they will most likely download malware onto their devices.

The current threat situation touches everyone. For soccer fans, we all have heard of this timeless admonition, “If it sounds too good to be true, it probably is“. Although a cliché, it’s great wisdom to live by nonetheless. Fans are urged to always be vigilant and cautious with installing unknown applications, browser extensions, add-ons or plugins, particularly those from suspicious, anonymous sources. It’s safest to stream the games through legitimate, reputable websites such as ESPN or BBC. For IT security leaders responsible for defining the company’s security defense system, the best protection against deceptive tactics is to be proactive as persistent threat must be counter with persistent and adaptive security. Begin layering your defense system that will provide you many ways of preventing attacks and managing network bandwidth. This includes:
1) Vigorously defend the endpoints as most network infections begin with a compromised user device. Enforce every device attempting to access the internet to have threat prevention capabilities such as content filtering capable of blocking inappropriate, illegal and dangerous web content.
2) Comprehensive gateway threat detection m services that can provide complete inbound anti-spam, anti-phishing and anti-virus protection.
3) Manage network bandwidth with application control capabilities to provide granular control of certain application–limiting or blocking access–by setting policies based on logical pre-defined categories (such as sports), individual applications, or even users and groups to keep business application running at full speed.
4) Breaking the malware kill cycle by investing in a capable intrusion prevention system because it is far easier to keep the bad guys out than to expel them.
5) Add SSL inspection and application control to detect and prevent today’s advance evasive tactics or compromised web applications from sneaking malware into the network.
6) And finally, ensure that there is a 24x7x365 threat response and counter-intelligence service for the firewalls and intrusion prevention systems so it can quickly receive the latest countermeasures to combat new vulnerabilities as they emerge.






