Panda Security, The Cloud Security Company, has announced the latest findings of the PandaLabs quarterly report for Q1 2014. The main conclusions of the study include the fact that malware creation has broken all records during this period, with a figure of more than 15 million new samples, and more than 160,000 new samples appearing every day.
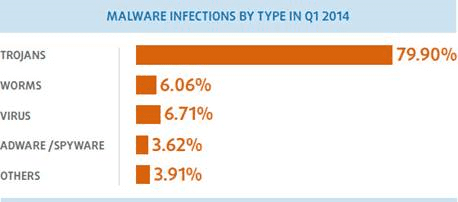
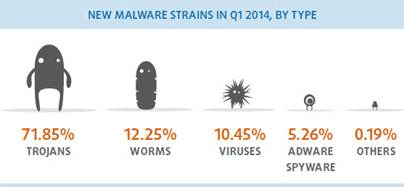
Trojans are still the most abundant type of new malware, accounting for 71.85% of new samples created during Q1. Similarly, infections by Trojans were once again the most common type of infection over this period, representing 79.90% of all cases.
In the area of mobile devices, there have been increasing attacks on Android environments. Many of these involve subscribing users to premium-rate SMS services without their knowledge, both through Google Play as well as ads on Facebook, using WhatsApp as bait.
Along these lines, social networks are still a favorite stalking ground for cyber-criminals, The Syrian Electronic Army group, for example, compromised accounts on Twitter and Facebook, and tried to gain control of the facebook.com domain in an attack that was foiled in time by MarkMonitor.
During the first three months of the year we have witnessed some of the biggest data thefts since the creation of the Internet, and as expected, Cryptolocker, the malicious file-encrypting ransomware which demands a ransom to unblock files, has continued to claim victims.
“Over these months, levels of cyber-crime have continued to rise. In fact, we have witnessed some of the biggest data thefts since the creation of the Internet, with millions of users affected”, explains Luis Corrons.
Trojans, the malware of choice for hackers
So far in 2014, Trojans are still the malware most commonly used by cyber-criminals to infect users. According to data from PandaLabs, four out of five infections around the world were caused by Trojans, that’s 79.90% of the total. Viruses are in second place, accounting for 6.71% of infections, followed by worms, with a ratio of 6.06%.
Trojans, the most frequently created malware
Trojans also top the ranking of newly created malware, accounting for 71.85% of the total, followed by worms, at 12.25%, and viruses at 10.45%.
Infections by country
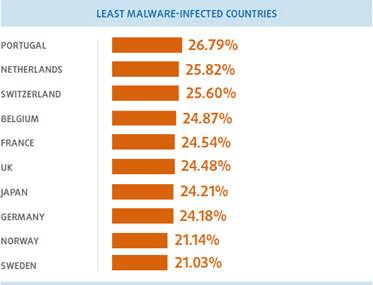
The global infection rate during the first three months of 2014 was 32.77%. China is once again the country with most infections, with a rate of 52.36%, followed by Turkey (43.59%) and Peru (42.14%). Although Spain is not in the top ten of this ranking, it is still above the global average with 33.57%.
European countries ranked high among the least infected countries, with the best figures coming from Sweden (21.03%), Norway (21.14%), Germany (24.18%) and Japan, which with a ratio of 24.21%, was the only non-European country in the top ten of this list.
You can download PandaLabs reports from: http://press.pandasecurity.com/press-room/reports/
About Panda Security
 Founded in 1990, Panda Security is the world’s leading provider of cloud-based security solutions, with products available in more than 23 languages and millions of users located in 195 countries around the world. Panda Security was the first IT security company to harness the power of cloud computing with its Collective Intelligence technology. This innovative security model can automatically analyze and classify thousands of new malware samples every day, guaranteeing corporate customers and home users the most effective protection against Internet threats with minimum impact on system performance. Panda Security has 80 offices throughout the globe with US headquarters in Florida and European headquarters in Spain
Founded in 1990, Panda Security is the world’s leading provider of cloud-based security solutions, with products available in more than 23 languages and millions of users located in 195 countries around the world. Panda Security was the first IT security company to harness the power of cloud computing with its Collective Intelligence technology. This innovative security model can automatically analyze and classify thousands of new malware samples every day, guaranteeing corporate customers and home users the most effective protection against Internet threats with minimum impact on system performance. Panda Security has 80 offices throughout the globe with US headquarters in Florida and European headquarters in Spain
Panda Security collaborates with The Stella Project, a program aimed at promoting the incorporation into the community and workplace of people with Down syndrome and other intellectual disabilities, as part of its Corporate Social Responsibility policy.
For more information, please visit http://www.pandasecurity.com






