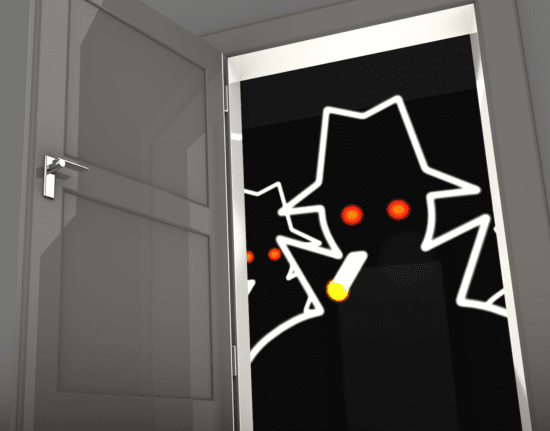
Security researchers at Check Point published research today, identifying a Remote Control Execution (RCE) vulnerability in Instagram. The attacker would only need a single, malicious image to execute the attack. Check Point researchers summarised the attack method to three steps:
- The attacker sends an image to a target victim’s email, WhatsApp or other media exchange platform.
- The picture is saved to the user’s mobile phone. This is can be done automatically or manually depending on the sending method, the mobile phone type, and configuration. A picture sent via WhatsApp for example will be saved to the phone automatically by default on all platforms.
- The victim opens the Instagram app, triggering the exploitation, giving the attacker full access for remote takeover
In effect, the vulnerability gives the attacker full control over the Instagram app and turns it into a spy tool with the power to create actions on behalf of the user: reading all direct messages on the Instagram account, deleting, or posting photos at will, manipulating account profile details. Since the Instagram application is known to have extensive permissions that are gateways to features and functionality on one’s phone, an attacker could use the vulnerability to access phone contacts, location data, phone cameras, and files stored on the device, turning the phone into a perfect spying tool. At the most basic level, the exploitation could be used to crash a user’s Instagram app, denying them access to the app until they delete it from their device and re-install it, causing inconvenience and possible loss of data.
Research details: https://research.
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.