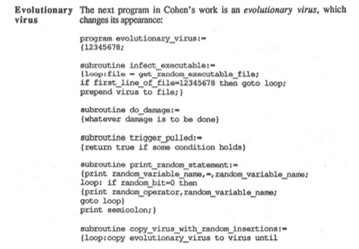
Travelling back to the early days of the Computer Virus entering the world of low cost, COTS (Commercial Off the Shelf) available computing, we may reflect on a few home truths as we proceed down the Road to Digital Perdition. Circa 1983 when Fred Cohen, a graduate student out of the University of Southern California presented his thoughts of the digital future of potential adversity, by demonstrating a computer virus during a security seminar at Lehigh University in Pennsylvania. See Fig 1. I recall that event very well, as it was not long after when the Sunday Times ran a small piece hidden in a corner of the paper on this discovery. Sadly however, at that time neither GCHQ or CESG considered this new digital phenomenon to be a risk worth breaking a sweat over – in fact their own words of the day were ‘We consider the computer virus to be a passing nuisance’. Shortly after 1984, we started to see the manifestation of computer viruses in the form of File and Boot Sector viruses start to impact computers far and wide across the Globe.
Fig 1 – Fred Cohen’s Evolutionary Virus
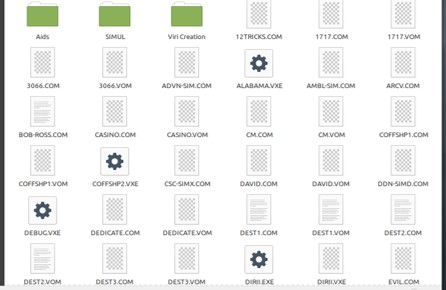
Those early day viruses appeared in many forms, Brain, Casino, Cascade, and many more – at Fig 2 is my early library of all the computer viruses I collected in that period of learning – all of which were taking their toll on those who were supporting corporate computer assets, and fighting off this new digital evil (or in the worlds of GCHQ – nuisance).
Fig 2 – Early Days Virus Library
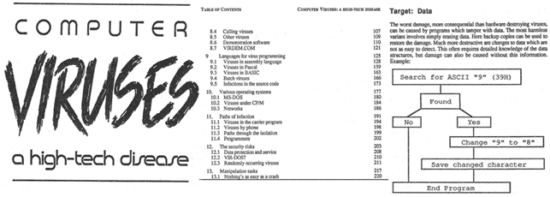
One of the next notable events from these early heady days of the Computer Virus was the publication of ‘Computer Viruses – a High Tech Disease’, authored by Ralf Burger, with its second edition being released in 1988 (See Fig 3 below).
Fig 3 – Computer Viruses – a High Tech Disease
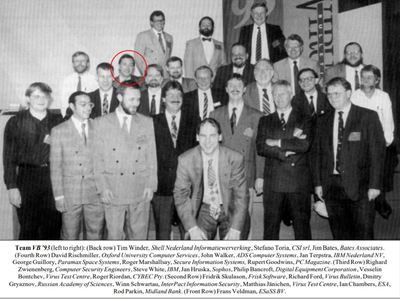
Around that time, I, like many others were reading Ralf Burger’s brilliant book and researching how computer viruses worked. I went on to write some new code for research purpose only, and to underpin a paper I was presenting at the Virus Bulletin Conference being held at the Grand Hotel Krasnapolsky in Amsterdam in 1993, subject of How to evade Anti-Virus Defences by cloaking the viral payload which would allow AV defences to be evaded – See Fig 4.
Fig 4 – VB93 – Amsterdam
At that time the machines to hand were 286, 386, eventually going up to the power of the 486 processor. Just like today, with the moto in mind, when I see it, I want to know how to break it – I looked for the weakest link, and this arrived in the form of COMMAND.COM. Post a few experiments, I reengineered the file and had a bit of fun – allowing a Directory to be created but removing the ability to remove the created directory. However, it soon became clear that here was a file that could be engineered to evil purpose, and again post a few versions, this ordinary everyday file was crafted into a very dangerous object. Today, we are very much in the same space, what is seen as a normal file or object by one person, can be seen as a potential to create an adverse digital condition by another – it all comes down to the imagination of the perpetrator, but in the year 2021 on a much more dangerous scale.
To appreciate the high impact implications of the dangerous computer code in the wild, we may look back to the world’s first global scale infections to find its way into the wild – The Morris Worm (Internet Worm) circa 1988, and whilst the damages of this worm were hard to evaluate, it is estimated that at the time, the financial consequences amounted to $100,000, eventually increasing into the $ million’s.
Coming right up to date, what we now face in 2021 makes what has gone before look like playthings – 27 June 2017, born out of a long, undeclared war with Russia, the Ukraine fell into a void of a large-scale cyber-attack in which nothing of a technical nature seemed to operate – those every ready ATM machines were no longer willing to pay out cash, trains and airports were affected, TV stations went off line, and even critical infrastructure suffered, with radiation monitors at the Chernobyl nuclear plant going down. As the event unfolded the infectious tentacles of this malicious code seemed to be spreading further afield than had been intended (as was also the case with Stuxnet). It travelled onward through Europe and around the planet, downing hospitals and companies in the UK, US with wide impact on transportation. Knock-Knock, Who’s There – the answer came back NotPetya. A couple of hours or so later, the infection spread of this malicious weapon turned tail, and went back to Mother Russia, but not before it had caused approximately $US10 billion ($12.9 billion) in global damage – the most expensive cyber-attack to be encountered to date.
Fact of the matter is, the day the US Administration created the Stuxnet Digital Weapon out of the NSA, we stepped one pace closer to the potential of global annihilation, turning what we call a Man-in-the-Middle Attack into a state of a Man-Exposed-in-the-Middle, in which ordinary citizens and businesses will suffer as the state of undeclared electronic warfare takes place in front of our daily lives.
There is now no doubt whatsoever, that the over complex wired world we live in has let a Genie of the bottle and having escaped we now have to appreciate that this little imp does not intend to go back inside that glass-cage. The world of 2021 and beyond must now plan to build and deliver robust systems, put continuity plans in place for what will come, and consider the consequences of an electronic state of epic proportions which will not only cost multiples of $ billions, but an event that will cost lives for certain. We have been warned, we must now act as we proceed down the Road to Digital Perdition!
‘The New Man-in-the-Middle Attack Exposure
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


