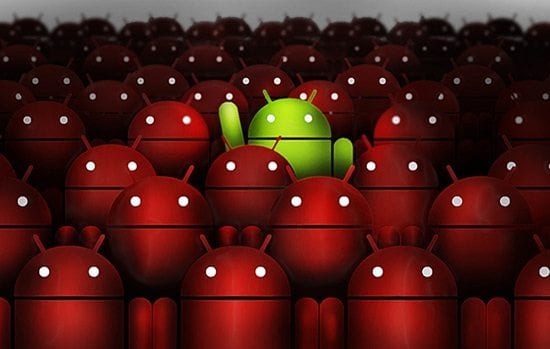
A new Android Trojan named “Red Alert 2.0” has been discovered and has targeted banks and social apps. Although it has some of the same capabilities as most other Android banking Trojans there are other functions that have not been seen in other Android banking Trojans. Josh Mayfield, Platform Specialist at FireMon commented below.
Josh Mayfield, Platform Specialist at FireMon:
 “In the context of enterprise BYOD (bring your own device), many organisations are using containers to control what a personal mobile device can do. This falls in line with the continued evolution of the identity becoming the new perimeter. No longer can one assume security with firewalls and intrusion prevention systems alone; people use their own devices, their own applications, and integrate their personal and work lives.
“In the context of enterprise BYOD (bring your own device), many organisations are using containers to control what a personal mobile device can do. This falls in line with the continued evolution of the identity becoming the new perimeter. No longer can one assume security with firewalls and intrusion prevention systems alone; people use their own devices, their own applications, and integrate their personal and work lives.
Mobile Device Management (MDM) can enable this trend by establishing policies for BYOD, reducing security risks associated with mobile devices. By containing and provisioning services on the mobile device, organisations can encircle the privileges of the device. This makes security management feasible, because it compresses the potential attack surface.
End user education is a critical in the evolving landscape and fuzzy perimeter. The average person is not going to be as well-informed about the threats or problems they face. Additionally, the typical Android BYOD user does not readily appreciate how their device could create a security concern at work. Security personnel often have a ‘curse of knowledge’ where they understand much more than their typical user; do not assume others know as much as you do.
Awareness of just how dangerous the world can be and how personal devices can bring down the enterprise can help users appreciate the stakes and take care when something like BYOD becomes standard.
Then, there comes the technical side of things. By automating policy management, organisations can establish access controls that mitigate risks posed from BYOD, especially mobile devices. Policy management is no longer an exercise of going to the firewall console and creating rules with the desktop and on-prem applications. This mobile world needs a better way to manage access required to keep thing moving at the speed of business – that’s why BYOD exists in the first place. Now that it’s here, we can manage our policies with automation and intelligence.
By regularly updating your applications and Android OS, users can take advantage of the patches and security fixes. MDM, for example, can prevent a user from getting on the organisation’s network from a back-dated device. This is a nudge in the right direction. You want to get on the corporate network? Make sure your device is updated with the latest security and OS patches.
This can be an automated function coming directly from policy management. By assessing devices and treating the identity as the primary source, our destinations and pathways can be secure. Organisations are too complex, permutations are too rapid to assess each individual case. Policy automation can address these challenges, preventing the infections from becoming an epidemic in the network.
Personally, I see the calls to social media and contact harvesting as a gateway to be more effective at social engineering. Phishing started with email communication between the user and a company or service – “Time to update your account!” Increasingly, malware is coming in the form of person-to-person relationships. If I can gain access to your social media accounts and contacts, I can discover who you are and the interpersonal connections you have. My phishing attack will be more effective.
The user may have learned not to execute a PDF sent from a bogus company, realising that this tactic is phishing. But imagine an email coming from a college friend. The friend asks for details about job opening at your company. This ambitious friend of yours asks you to look at their resume (attached) or to click on the link which will take you to their portfolio online. And….execute malware.
With identity becoming the new perimeter, it is vital for attackers to know those identities inside and out. The more I can discover about your identity and personal connections, the better I can exploit you.”
The opinions expressed in this post belongs to the individual contributors and do not necessarily reflect the views of Information Security Buzz.