Malware called Gameover, Zeus, GOZeus, or P2PZeus has been created by Cyber Criminals and is in active circulation as of June 2014 and is classified as a credible and SIGNIFICANT & CRITICAL THREAT.
This is very aggressive Malware code infects systems [PC’s, Servers etc.] in order to recruit them so that they may be utilised and controlled by Cyber Criminals under what is referred to as a BotNet, associated with centralised, or distributed Command and Control Systems – The BotMaster(s).
Upon any such computer asset being subject to compromise by this malware the attacker can then potentially carry out a number of remote and unauthorised actions such as:
– Viewing SENTITIVE AND PRIVATE FILES
– Accessing information relating to Bank Account, and other such on-line financial transactions
– Sending emails from your system/account
– Invoking the attached Web Cam to visually infiltrate personal space
– Potentially launching using your system to launch a Distributed Denial of [DDoS] Service Attack
– And possibly active other attached devices, such as sound/microphones
This strain of Malware is also associated with what is referred to as Ransomware which Cyber Criminals can leverage to prevent the authorised user from accessing their own files by locking them down. However the attacker [Cyber Criminal] may offer the infected system owner the opportunity to pay to regain access to such locked files, but there is no guarantee that the locked systems will be unlocked once the transaction [payment] has been made.
This attack is also associated with the distribution and communication of email which may claim to be from your bank, or other government agency such as the Inland Revenue and Customs urging you to check your account, or to claim an outstanding refund – these are what we refer to as Phishing emails.
Such communications may also carry an attachment or link back to what looks to be a legitimate website – however if you open such attachments, downloaded, or visit the associated website there is a very HIGH RISK that the system [your computer] will be infected, and compromised.
Also be aware that you may receive an email offering you protection in the form of free Anti Malware software – these also may be Trojans which are seeking to compromise your systems – DO NOT DOWNLOAD or USE.
To secure your family, business, and the associated information and assets apply the following recommendations:
– DO – Ensure your computer and associated applications are fully up-to-date with the latest vendor patches and updates
– If you systems support – DO ensure that Auto-Update is enabled
– DO ensure that your Browser is up-to-date with the latest patches and fixes
– DO ensure your systems is accommodated with a Personal Firewall
– Above all – DO ensure you are running a robust Anti Malware protection in a fully up-to-date state
– DO NOT Open or access any suspicious looking mails
– DO NOT Download any Attachments of files – these may be Trojans
– DO NOT go to any suggested or suspicious looking website 
Remember – if you or your organisation are operating out-of-support system [e.g. Windows XP], then you are at a higher risk, as these systems will no longer be issued with updates.
Note 1: Unless you are a commercial which as subscribed to extended support.
Note 2: It may also be that where practical using more secure cut-down-browsers will also assist to reduce the threat of localized system compromise and incursion. One example is the Aviator Browser – See URL below for more information:
https://www.whitehatsec.com/securebrowser
There is much recent hype about this new threat. However, this is but one of many long standing projects that have been run by the Cyber Criminal fraternity, and have not just evolved over the last few weeks, but has been in the making over a sustained period supported by powerful software applications known as BlackShades, and other such RAT [Remote Access Trojans]. See Fig 1.
Fig 1 – BlackShades
Fig 2 below shows that the sites have now been taken off-line by the FBI. However, it should be noted that multiple copies are still in circulation, and these tools can still today by obtained from the DarkNet.
Fig 2 – BlackShades Site Seized

So take proactive steps, and get the security baseline in place – the following are valid and trusted sources to obtain Anti Malware Protection from:
Kaspersky – http://support.kaspersky.com
Symantec – http://www.symantec.com
F-Secure – http://www.f-secure.com
Sophos – http://www.sophos.com
McAfee – www.mcafee.com
Trend Micro – www.trendmicro.com
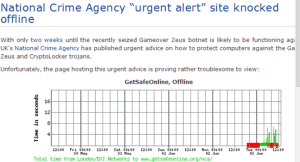
It is also interesting that whilst we [[the [public] have been provisioned with some systems to notify alerts, under the strain of reporting, and public/company access these resources collapsed – but this does tend to demonstrate the public interest. Or the opposing question is of course, where these systems also subject to attack and/or compromise by the Cyber Criminals? – See Fig 3. And at Fig 4 the NCA also of-line.
Fig 3 – GSOL Down
Fig 4 – NCA Down
It would be a mistake to see the current adverse situation as a one-off, and ISX recommend that the aforementioned practices are not just applied for the current threat, but that they are applied as a matter on on-going baseline security.
And as for the concept of 2 weeks to prepare and get secure, I am unsure where this assessment out of the NCA came, and can only conclude this is the new concept of the ZeroDay+14 notification system. Clearly the bad guys are now playing to the rules!
Professor John Walker FMFSoc FBCS FRSA CITP CISM CRISC ITPC
Visiting Professor at the School of Science and Technology at Nottingham Trent University (NTU), Visiting Professor/Lecturer at the University of Slavonia[to 2015], CTO and Company, Director of CSIRT, Cyber Forensics, and Research at INTEGRAL SECURITY XASSURNCE Ltd, Practicing Expert Witness, ENISA CEI Listed Expert, Editorial Member of the Cyber Security Research Institute (CRSI), Fellow of the British Computer Society (BCS), Fellow of the Royal Society of the Arts, an Associate Researcher working on a Research Project with the University of Ontario, and a Member, and Advisor to the Forensic Science Society
The opinions expressed in this post belong to the individual contributors and do not necessarily reflect the views of Information Security Buzz.


